You have numerous options when it comes to data loss prevention (DLP) solutions. Investing in the right one for your company will help you to strengthen the security of your business and better ensure the trust your customers place in you is justified. In this article, I review the best DLP software available on the market today designed to help mitigate data breach risks.
Best DLP Software Comparison
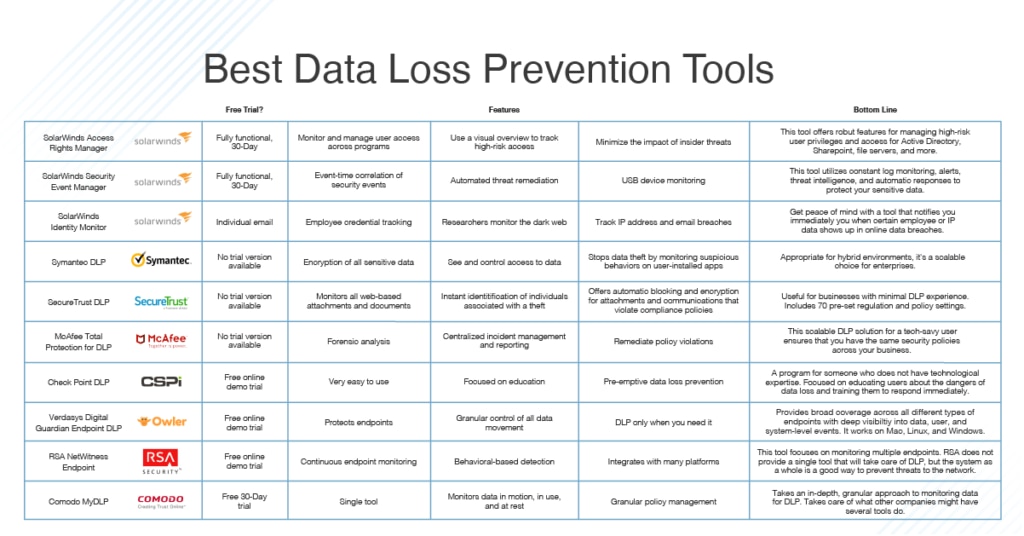
Feel free to jump ahead to each tool description:
- SolarWinds Security Event Manager (SEM) – my pick
- SolarWinds Access Rights Manager (ARM)
- SolarWinds Identity Monitor
- Symantec Data Loss Prevention
- Digital Guardian Endpoint DLP
- McAfee Total Protection for DLP
- SecureTrust DLP
- Check Point DLP
- Comodo MyDLP
- RSA NetWitness Endpoint
The market is full of data loss prevention tools and trying to find the right one can be overwhelming. I’ve spent hours investigating the many software options available, and a few stand out for their comprehensiveness and ease of use. While all the tools I’m recommending are paid, some have free trials. I found open-source DLP solutions simply don’t provide the same rigorous level of protection, and they’re not sufficiently reliable to be trusted with your most important asset: your customers’ data.
-
SolarWinds Security Event Manager (SEM) [Free Trial]
SolarWinds offers two of the best data loss prevention software on the market. While both provide excellent data protection against data loss, I’m ranking SolarWinds® Security Event Manager slightly above SolarWinds Access Rights Manager (more on this tool below) because it includes USB Defender, which protects one of the most vulnerable—and most overlooked—points on a network.
© 2023 SolarWinds Worldwide, LLC. All rights reserved.
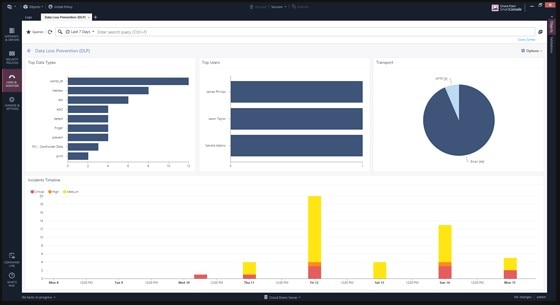
SEM takes the hard work out of protecting your sensitive data through constant monitoring across your network. It collects, centralizes, monitors, and analyzes user activity logs, so you can get visibility into the actions of all the users on your network, with real-time reporting if any of those actions violate your business’s policies.
One of the best things about SEM is it makes reacting to threats easy with its automated responses. While the software comes with built-in templates for rules and responses to insider threats, it also gives you the opportunity to easily make your own rules for automatic responses to the threats your business is most concerned with.
This brings me to the USB Defender feature. USBs are some of the easiest points through which to steal data, because they’re often unmonitored, or at least not heavily monitored. With USB Defender, all USBs on your network are not only secured by suspicious activity monitoring, but are also supported by the active-response technology central to SEM. This is a huge advantage in protecting sensitive data against threats posed by end users.
SolarWinds SEM installs on Windows Server and complies with security standards including PCI DSS, HIPAA, and SOX. You can download a 30-day free trial to test out the fully functional software for yourself.
Access control is an incredibly important part of DLP, since many data breaches are caused by someone with insider access to the system. SolarWinds Access Rights Manager comes with a user-friendly interface to help you easily identify who has access to what data, so you can respond as quickly as possible to any cybersecurity threat.
© 2023 SolarWinds Worldwide, LLC. All rights reserved.
SolarWinds describes ARM as “security simplified,” which I find to be an accurate description of this data loss prevention tool. With clear reports and identification and the ability to monitor high-risk accounts, you’re equipped to make sure no one is accessing information they shouldn’t. Through monitoring for Active Directory, OneDrive, Windows file share, SharePoint, and Microsoft Exchange, ARM can also help you identify any user who has displayed suspicious activity across multiple communication channels.
All these insights make it easier to adjust your access policies. You can then use ARM to set and implement better data access controls and to see if anyone is trying to change access controls in Active Directory or Group Policy. ARM goes above and beyond the access control provided by other software programs to analyze users on a deeper level, studying their credentials and analyzing how they use those credentials to gain data access. It alerts IT teams of suspicious activity indicative of a data breach, so they can act to prevent data loss.
ARM installs on Windows Server and provides auditing and reporting compliant with HIPAA, PCI DSS, and GDPR. As with SEM, you can also try the full software free for 30 days.
SolarWinds Identity Monitor essentially provides you instant insight into whether your employees’ credentials, like logins and passwords, have shown up in data breaches. The tool is designed to track enterprise data leaks across the “dark web,” providing insight into both current and past security breaches. It can even track email account information for your key employees to help prevent scams. Identity Monitor is also useful for IP address tracking—you can add IPv4 or IPv4 network CIDR to the platform’s “watchlist,” and the software will look for this information automatically.
© 2023 SolarWinds Worldwide, LLC. All rights reserved.
If credentials or other key company data does show up on the tool’s radar, Identity Monitor is designed to notify you quickly. This speed is critical for preventing data loss and dangerous account takeover. By choosing Identity Monitor, you get an extra level of protection without having to put manual effort into combing through company data breaches yourself. For peace of mind, SolarWinds Identity Monitor is a worthy investment.
Broadcom Data Loss Prevention (previously Symantec) is enterprise oriented, meaning while it’s scalable to a smaller business, it may be unnecessarily complicated for small business use. If you’re looking for DLP software for a large enterprise, however, this tool provides helpful services.
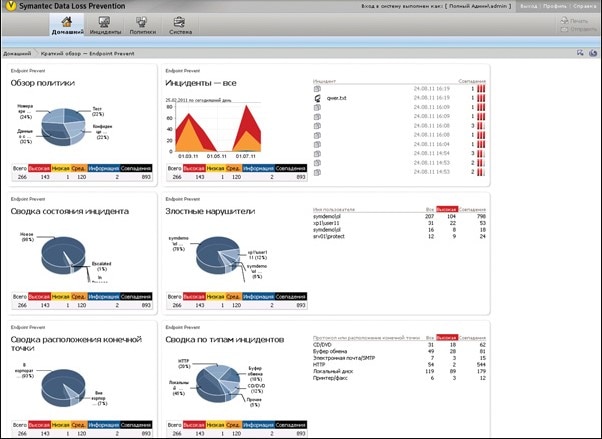
Copyright © 2005-2023 Broadcom. All Rights Reserved.
Broadcom DLP software is part of its endpoint data protection system. The tool provides great coverage throughout your business—in the cloud, on mobile devices, and on multiple endpoints, including desktops and servers. It comes with a management dashboard, so you can identify apps trying to access secured information and prevent them from doing so. The dashboard also lets you stop non-compliant data transfers.
When Broadcom DLP is first installed, it conducts a sweep to find all the sensitive data in your network. It then gives you the option to either store the data in place or move it to a secure central data repository. It also encrypts all sensitive data, logging the access to the data and destroying all retired copies and discarded documents, avoiding their accessibility by hackers. With Broadcom DLP you can control who has access to sensitive information, including through fingerprinting recipients to confirm they are meant to have access to the information sent to them.
Broadcom DLP doesn’t offer a free trial version, nor does it include an easy reporting function for audits. It’s also worth noting some users complain the dashboard is too rigid.
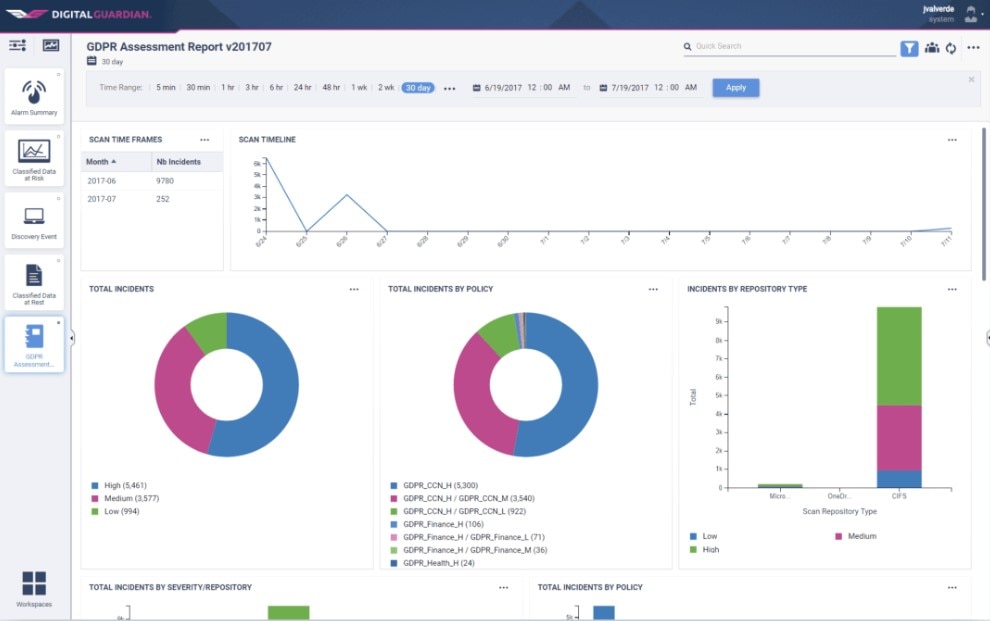
Copyright © Fortra, LLC and its group of companies.
Digital Guardian Endpoint DLP has a lot of great elements, and while it takes considerable work to set up to reach its maximum capabilities, once the work is done, it’s a powerful DLP tool. This makes it better suited for larger enterprises than for small businesses, which are less likely to have the manpower to invest in getting it up and running.
This solution works on Mac, Windows, and Linux systems to monitor data on-premises as well as in the cloud. It can be set to automatically block, justify, or encrypt sensitive data. You can also set it to automatically block user activity based on the contexts you determine to be suspicious, and then to log and audit the event for forensic analysis.
Some users report Endpoint DLP gives excessive false positives, resulting in alerts for non-critical events, and it sends out frequent updates to fix one problem but cause another.
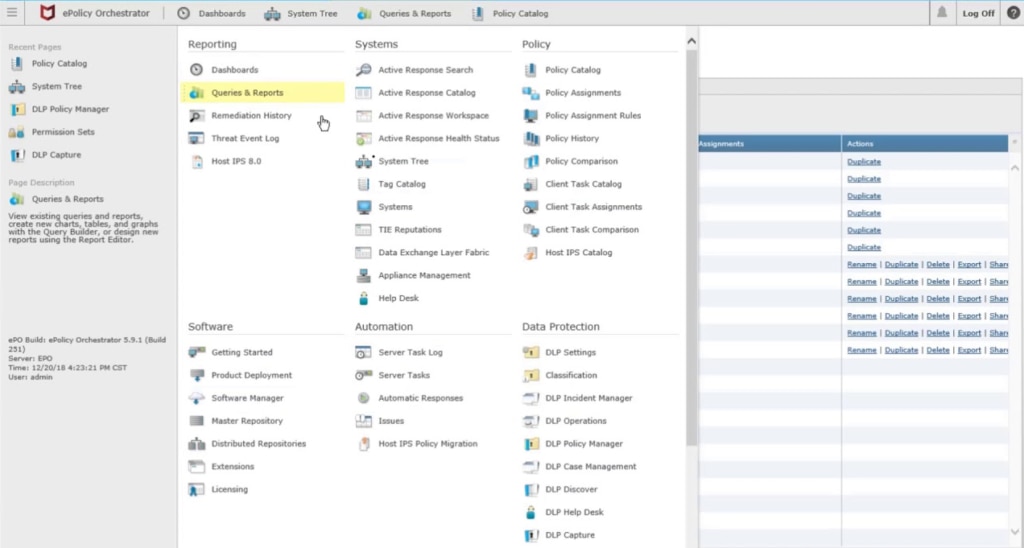
Copyright © 2023 McAfee, Inc. All Rights Reserved.
McAfee Total Protection for DLP is a suite of multiple data protection tools. The software focuses on detailed forensic analysis and, unlike some DLP tools that treat all sensitive data in the same way, identifies and prioritizes more sensitive data.
McAfee’s DLP program also ensures you have the same security policies employed across your network, including on-premises networks, endpoints, and the cloud. The program is scalable, but it’s not as user-friendly for beginners as some other data loss prevention solutions. People say the settings are a bit complex and can be confusing if you don’t have experience with similar software.

© 2023 SecureTrust, Inc. All Rights Reserved
SecureTrust DLP is one of the best data loss prevention software available for businesses with minimal DLP experience, or that prefer preconfigured policies for what constitutes a violation or suspicious behavior. The tool is part of a suite from SecureTrust and, while it works on its own, it works better in conjunction with the company’s SIEM tool.
SecureTrust DLP comes with more than 70 predefined risk and policy settings you can easily turn on or off based on the needs of your business, making it usable right out of the box. However, for businesses wanting to set their own policies, the need to sort through all the existing settings can be a source of frustration.
SecureTrust DLP gives attention to analysis. It monitors all web-based attachments and documents—including emails, social media posts, and blogs—coming into your business, checking for violations of company governance, acceptable-use policies, and compliance. Attachments in violation are then automatically blocked.
©1994- 2023 Check Point Software Technologies Ltd. All rights reserved.
Check Point DLP is a great choice for anyone who has little to no understanding of data loss prevention strategy. It’s easy to use and comes with some preconfigured rules. If you’re better acquainted with data loss prevention, you may find this tool a little too simplistic. I’d recommend sticking with one of the tools higher up on this list.
The biggest point of difference between Check Point’s data loss prevention software and the others I’m highlighting is it puts a premium on educating your employees about the risks of data loss. One of the biggest factors in data loss, and one of the most difficult to prevent through technological solutions, is human fallibility, with employees often innocently introducing viruses into the system or sharing sensitive information with hackers. Check Point’s focus on education aims to teach employees to be more careful with data and to better identify and respond to incidents.
Beyond the education component, Check Point tracks and controls sensitive data across services, including email and web browsing, even when the data is in motion. The tool is managed across the entire network from a single console.
Copyright © 2023
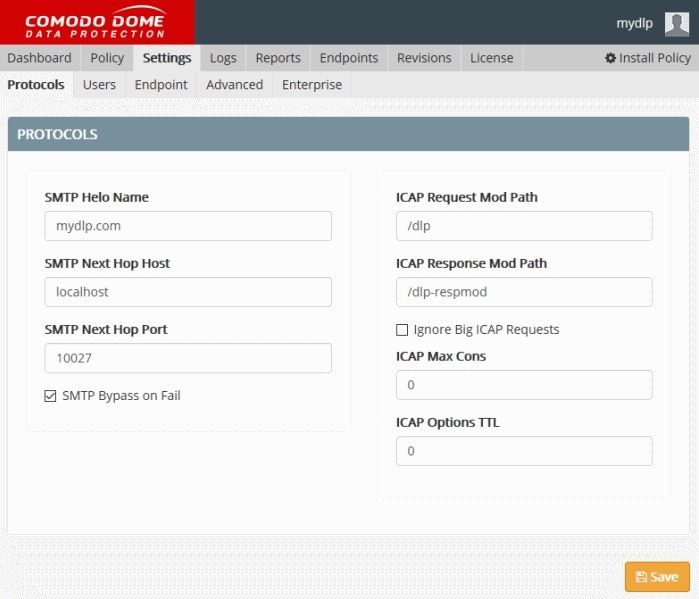
Comodo MyDLP is an all-in-one tool covering all your sites and endpoints as well as all your data, which is stored on a cloud server. This software logs and protects your sensitive data and engages in whitelisting/blacklisting to determine whether users have access to sensitive data. For those users with data access, it determines what actions they can conduct with the data.
This DLP tool protects endpoints along with the rest of the network. It can be set to block data flow containing sensitive information, meaning the information is prevented from leaving your system. It’s user-friendly, and it can either be accessed through the cloud or installed on-premises.
Though MyDLP is a broadly useful tool overall, I’ve heard complaints of it not doing a good job of identifying sensitive information in the first place. It also generally doesn’t go into as much depth in its analysis of suspicious behavior and security risks as other tools, which means it’s lacking in terms of incident management if a data breach occurs.
© 2023 RSA Security LLC or its affiliates.
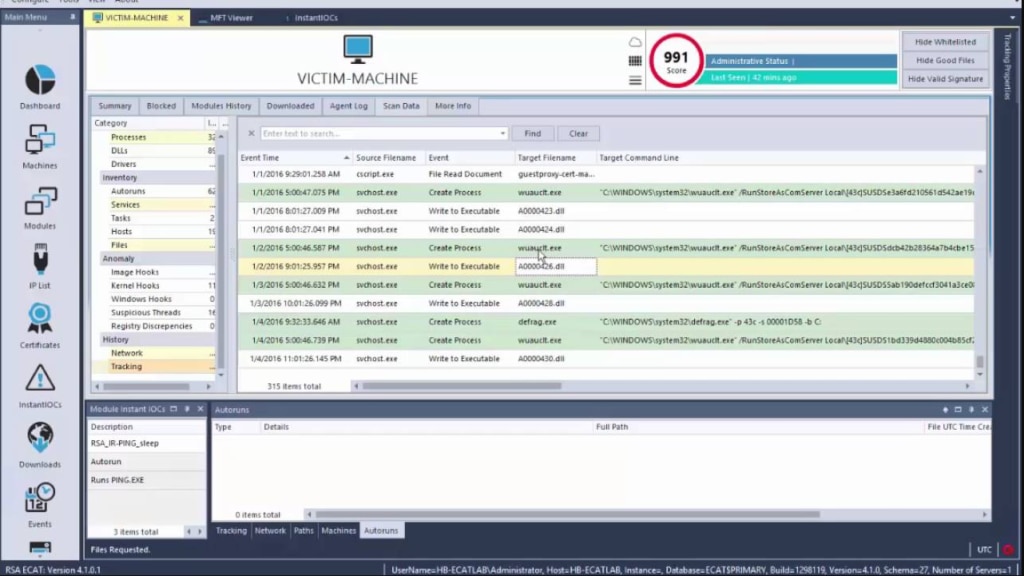
RSA NetWitness Endpoint can help with data loss prevention through its focus on endpoint monitoring. RSA’s weakest point is it’s not a single tool dedicated to DLP; rather, NetWitness Endpoint is part of a larger set of tools working together to protect your sensitive data. When combined with other RSA SIEM solutions, NetWitness can be a powerful data loss prevention tool, though not necessarily as robust as others closer to the top of this list.
RSA’s DLP tool focuses on endpoints, using behavioral monitoring and machine learning to continuously monitor those endpoints and isolate threats, and sending alerts in case of suspicious activity. The software prioritizes threats and provides analysis to help you get to the root of those threats.
The problem with this solution is maximizing its potential requires a major time commitment on the front end. Purchasing the tool gives you access to webinars, and you’ll need to be willing to devote a good amount of time to those webinars to get a solid grasp of the software.
Definition of Data Loss Prevention
Data loss prevention (DLP) refers to the process of safeguarding data to protect it against thefts and leaks. This is typically done through software identifying and monitoring sensitive data to ensure only authorized users are accessing it. DLP tools also help ensure those authorized users aren’t putting the data at risk, whether intentionally or unintentionally.
Essentially, data loss prevention tools control access to your company’s data and keep it from leaving the set perimeter of your network. DLP solutions do this either through identifying violations of the predefined policy packs included in the software, or by identifying violations of access policies set by the organization.
DLP tools build a context around your sensitive data to help you determine how best to approach prioritizing, protecting, locking down, and monitoring your data (like important intellectual propery data) to prevent breaches. They’re especially beneficial given the increases in the intensity of state privacy laws focused on increased data protection and access control in response to the ever-present threat of hackers, who can use the data they steal for financial fraud and identity theft. DLP software usually includes reporting functions to help you meet auditing and compliance requirements and make sure you don’t incur fines for failing to protect your customers’ data sufficiently.
Why Is Data Loss Prevention Important?
Your customers’ sensitive information is your business’s most valuable possession. When they give you their private information, customers are trusting you to take every measure possible to protect it. Without sensitive data loss prevention tools, you run a serious risk of losing customer data, leading to potential identity theft, financial fraud, and, most importantly, loss of trust.
In the past several years, high-profile data breach incidents led to people across the country having their personal information stolen. These events should have been preventable had the organizations in question used DLP software. The frequency of data breach events is such that the internet is full of pages listing data loss events organized by year and month. No matter the size of a business, the impact of data breaches can be devastating, causing both financial losses and losses to reputation, and could cause the business to fail.
It’s easy to think data leak won’t affect you, but any business is a potential target for hackers. While we typically hear about major data breaches, like the 2019 Facebook breach where the personal information, including unique user IDs and phone numbers, of 419 million users were exposed, data leakage on some scale happens constantly. Often, the hackers don’t even have to work hard to achieve their goals. In the Facebook example, the hackers simply discovered an unprotected server and were then able to access all the data it contained.
While Facebook is a large enough institution to recover from a breach of this magnitude, most businesses aren’t as integral a part of society as Facebook is today—which means it’s much easier for customers to take their business elsewhere if they become concerned about the security of their information.
Most IT-specific compliance regulations for sensitive data protection require auditable DLP to prove you’re taking all the necessary steps to protect your customers. As noted above, endpoint data loss prevention tools typically provide auditable reporting capabilities to demonstrate the software is compliant with regulations including SolarWinds Security Event Manager designed to comply with PCI DSS, HIPAA, SOX, and more.
Managing Access Control to Prevent Data Loss
Intellectual property loss and data breaches can be the result of some action taken by an insider, whether intentional (like a disgruntled former employee putting sensitive information onto an external hard drive to sell to a competitor) or unintentional (as when an employee finds a flash drive and plugs it into their computer to find out what’s on it). For this reason, one of the core components of data loss protection is managing access control, which means monitoring and controlling who have sensitive data access and what they can do with it.
Rather than try to manually monitor user activity on your own—an endeavor likely to become overwhelming—I advise implementing a data loss prevention tool engaged in access control. Good DLP software not only monitors access on your network but also alerts the administrator to any violations of your access policies, whether those policies are set by your business or come preconfigured with the tool. What’s more, the insights gleaned by a DLP tool with access control capabilities can be leveraged to adjust your access policies. Knowing who’s accessing the data on your network is important not only for preventing attacks that might result in data leakage, but also for decreasing the impact of fraudulent action in case a cyberattack does occur. Managing access control involves monitoring the behaviors of users on the network, including what data they are accessing. As a result, when there’s a data breach, administrators have a record of information they can consult to quickly pinpoint where the attack occurred and what users or devices were involved.
Verizon’s 2018 Data Breach Investigations Report showed the 24 hours after a cyberattack is a critical period in which the impact of the attack can at least be mitigated. For example, in the case of a financial attack, if the action of the attack is delayed during these “golden 24 hours,” it becomes unlikely for the hackers to be able to attain the funds they’re after. In short, the ability to respond to an attack quickly is critical to preventing data loss.
Leveraging User Activity Logs to Prevent Data Loss
Logs are one of the most important assets for an IT administrator when trying to discover the cause of a problem in the network or on a device. When it comes to data loss prevention, user activity logs continue to be a crucial asset.
Given the importance of speed in responding to outside and insider threats, user activity logs are most useful when you have a DLP tool actively monitoring, centralizing, and reporting on those logs in real time. Specifically, when you implement data loss prevention software with combined activity log monitoring and automated responses for disabling accounts, changing privileges, and blocking USB devices, you significantly simplify the process of threat remediation. Through comprehensive monitoring tracking every event on the devices across your network, you’re taking one of the strongest steps possible to protect your data.
How to Choose the Best DLP Solution
When making a data loss prevention solution comparison, take time to think through which features will be most valuable based on the needs of your business and what you consider to be the main threats to the security of your data. Although all the tools on this list seek to protect your sensitive information, their focus and strengths vary.
While different DLP devices approach their monitoring and analysis in different ways. I find the deep forensic analysis you get with SolarWinds SEM to be extremely helpful for ensuring your access policies are sufficient to protect your data. Equipped with this type of analysis, you can make sure any users who have access to your sensitive data absolutely require it—an essential step, since every point of access is an opportunity for a data breach.
