SIEM solutions are crucial for log management and comprehensive security. Here is the best SIEM tools list for businesses looking to add to or upgrade their solutions.
—————————————————————————————————————————————
Security information and event management, or SIEM, provides insights into a corporate IT environment through functions like log and security information management. Only the best SIEM software offers comprehensive security features, which every business can benefit from. When choosing a SIEM tool, look for features like compliance reporting, threat detection, historical log analysis, a user-friendly dashboard, and sophisticated analytics capabilities.
To help you choose the ideal SIEM solutions for your business, I have reviewed fifteen of the best SIEM tools in the market today. I start with my favorite option, product that balance affordability with full features – SolarWinds Security Event Manager. Check these out for great log management and strong security. Beyond this, there’s a crowded playing field — so I’m here to share the basics of what you need to know about an array of the best SIEM tools. With that being said, here are my picks for top SIEM products. Jump ahead:
1. SolarWinds Security Event Manager (Best Pick)
What Is Security Information and Event Management?
A Security Information and Event Management (SIEM) tool is software that provides insight into an organization’s information security landscape. It intersects Security Information Management (SIM), which collects, analyzes, and reports log data from various sources, and Security Event Management (SEM) which monitors and correlates events and notifications.
SIEM tools help organizations detect, analyze, and respond to security threats.
A SIEM tool is best if your organization wants to establish an effective cybersecurity protocol. Security Information and Event Management (SIEM) tools, which have been around for over a decade, are the most effective way for organizations to protect sensitive data. Larger enterprises are the primary customers for SIEM tools since they are the most likely to require IT oversight. However, small and mid-sized businesses (SMBs) can still enjoy the benefits of SIEM capabilities — often through a partnership with a managed service provider (MSP).
Key features of SIEM tools include:
- Log management
- Event analysis and correlation
- Detection and alerting
- Compliance and reporting
- Dashboard and visualization
Not every SIEM tool includes every function — a SIEM product can describe separate functions like log management, security log and event management, security event correlation, and security information management. Further, businesses are increasingly choosing SIEM products because they can help them align their security strategy with specific compliance frameworks like HIPAA.
For more details, see this article: What Is SIEM Software? Definition, How It Works, and How To Choose the Right Tool
How Do SIEM Tools Work?
SIEM tools function by collecting and aggregating log data. A SIEM solution analyzes security alerts from all applications and hardware across a network — from antivirus tools to servers to firewalls. These more targeted tools alone aren’t enough to protect a business — only a SIEM tool can give you a “big picture” understanding of your cybersecurity threat landscape. SIEM systems can detect and defend against active threats, but they also analyze logs for insights into anomalies and attacks after the fact, giving you the “why” behind an event.
Why Are SIEM Tools Important?
SIEM tools are proving to be more important than ever, as it has become undeniably useful to draw together data and threats from across your IT environment into a single, easy-to-use dashboard. Here are some reasons why SIEM tools are important:
- SIEM tools help organizations make sense of their log data by aggregating, normalizing, and analyzing it.
- By comparing seemingly unrelated events from many systems, SIEM technologies can help uncover intricate attack patterns that might be missed when examining individual events alone.
- SIEM tools provide extensive logging, auditing, and reporting features that assist organizations in meeting compliance obligations.
- Using SIEM tools, an organization can monitor and secure its IT infrastructure—which includes on-premises systems, cloud services, and hybrid environments—from a single, centralized platform.
- Advanced SIEM tools that have SOAR (Security Orchestration, Automation, and Response) features enable the automation of routine response activities, such as blocking an IP address or quarantining a system.
- By integrating external threat intelligence feeds, SIEM tools enhance an organization’s ability to identify emerging threats and known indicators of compromise (IOCs).
- SIEM tools can quickly identify potential security incidents or anomalies by continuously monitoring and analyzing data from various sources in real time.
What Is the Best SIEM Tool?
The best SIEM tools adeptly use past trends to differentiate between actual threats and legitimate use, enabling you to avoid false alarms while ensuring optimal protection. Ultimately, there’s no reason to be stuck with a suboptimal tool when so many powerful options are widely available.
Here’s a list of top SIEM tools:
1. SolarWinds Security Event Manager (Free Trial)
SolarWinds Security Event Manager provides all the log management features you need: security event-time correlation,compliance reporting, and advanced analytics features. It’s built for businesses that are specifically looking for robust log monitoring and better prioritization and response for incident management.
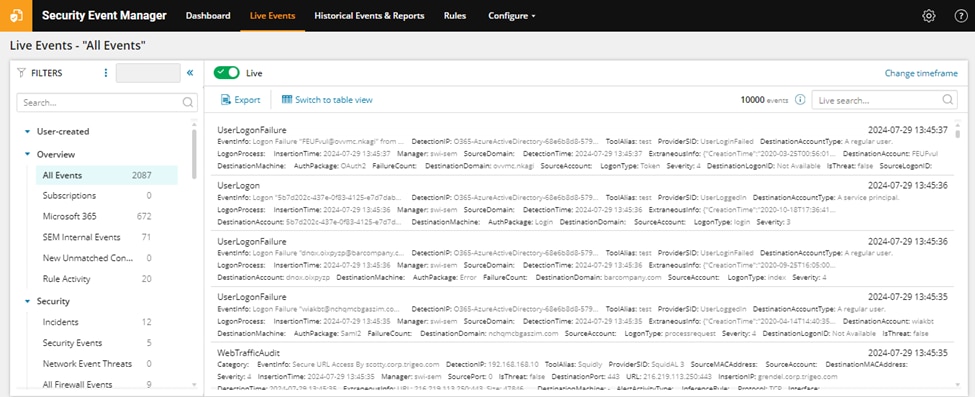
©2024 SolarWinds Worldwide, LLC. All rights reserved.
You can also use the tool’s file integrity checker to track access and other changes to files and folders — a nice bonus. This platform lets you customize and improve security with data encryption, SSO/smart card integration, and the ability to block IPs, applications, and USBs as needed. Plus, you get a fully functional 30-day free trial.
2. Micro Focus ArcSight ESM
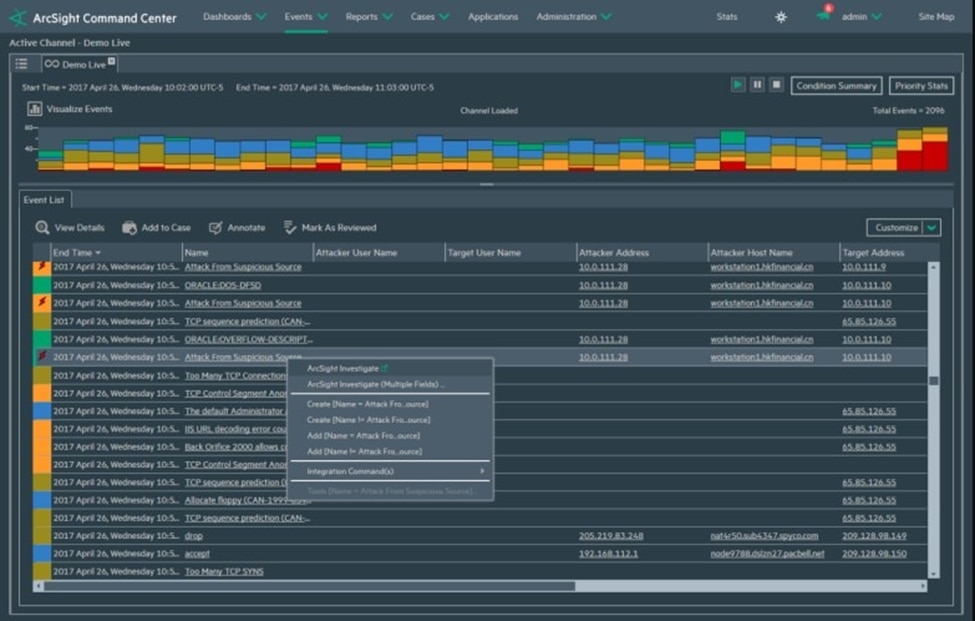
© 2024 Open Text
ArcSight by OpenText is a robust SIEM solution with an open architecture, giving it a few standout capabilities. This tool stands out because it can ingest data from a wider range of sources compared to many SIEM products, and expert IT teams may find it useful to use its structured data outside of ArcSight.
Its key features include advanced threat detection, comprehensive compliance, scalable architecture and integration with various security tools. ArcSight is highly customizable and optimized for efficiency, which helps you reduce ownership costs. Despite this, ArcSight may require complex deployment and management.
3. Splunk Enterprise Security
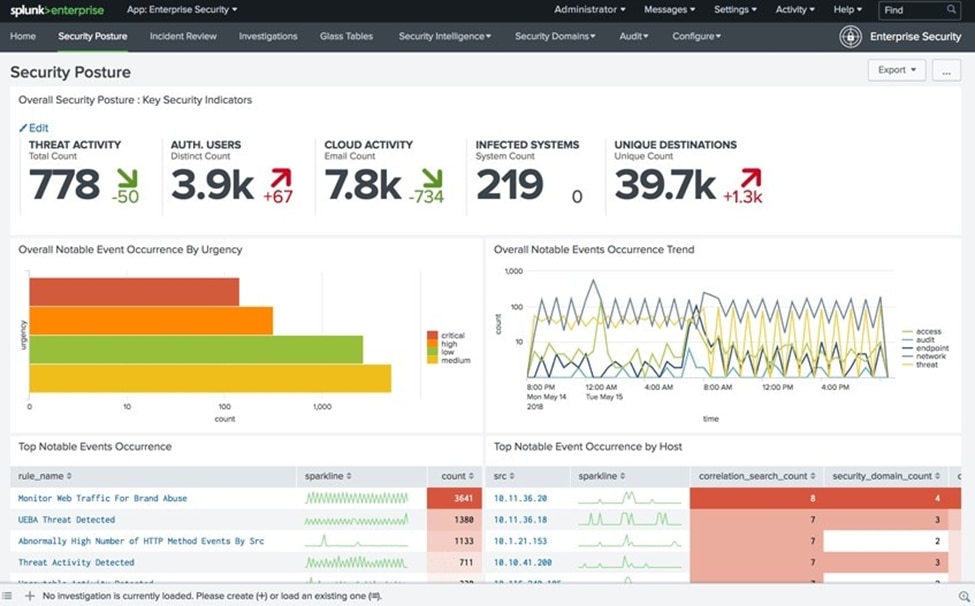
© 2005-2024 Splunk Inc. All rights reserved.
Splunk Enterprise Security is a popular option that has been around for over a decade. As the name implies, this is an enterprise-level option, which means the licensing costs aren’t particularly competitive — this tool may be too pricey for some. You can use this tool as on-premises software or a SaaS solution (ideal for AWS users). The dashboard has useful visualizations, like graphs and charts. It supports as many plugins and third-party integrations as you’re likely to need. That said, the learning curve can be steep if you’re looking to take advantage of deeper analytics features.
4. LogRhythm NextGen SIEM
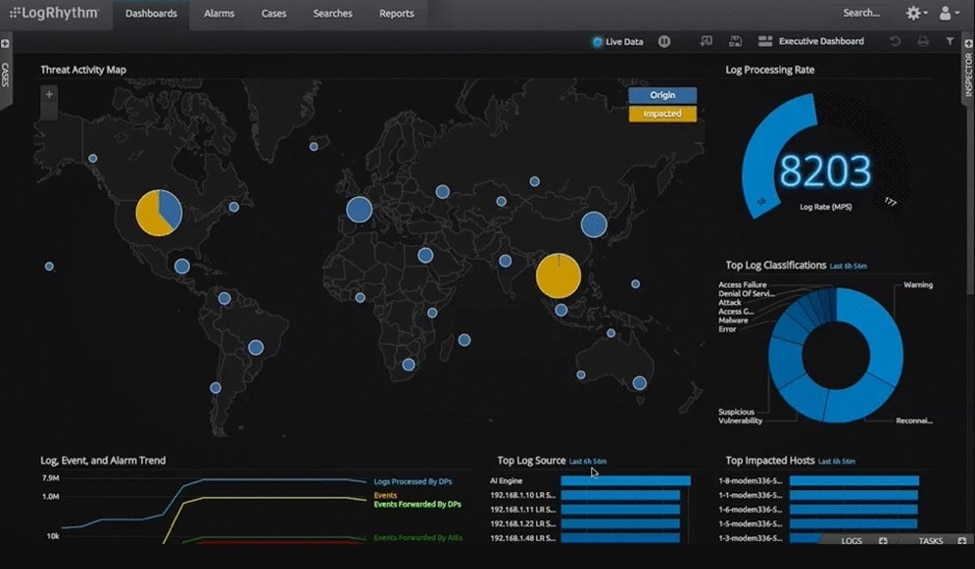
Copyright © 2024 LogRhythm, Inc. All Rights Reserved
This is a solid, fast option for critical log management on Windows. The tool is easy for trained IT staff to deploy, and the dashboard helps simplify workflow. If you have specific compliance standards and know your queries, it’s quick to configure the reports you need. This tool has rapidly evolving AI and automation features, which isn’t the case with every tool. All this being said, this platform doesn’t scale particularly well for larger businesses, and there’s limited support if you need to expand into cloud environments.
5. IBM QRadar

© Copyright IBM® Corporation 2017, 2024.
Businesses looking to integrate a wide range of logs across their critical systems will likely find QRadar reliable. Plus, this IBM product has smart features that catch diverse ever-changing threats. It’s not necessarily the most intuitive product, as it has a complex architecture to match its capabilities. For instance, setting alerts in QRadar can be a bit cumbersome. Of course, IBM products come with the higher price tag you would expect, but enterprises with extensive log management needs should consider this solid option.
6. Sumo Logic
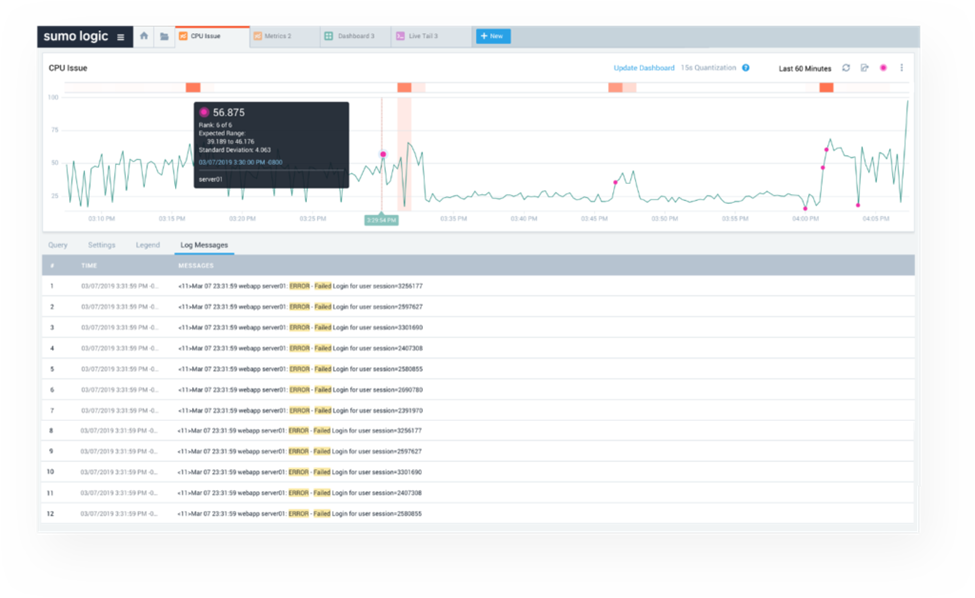
©2024 Sumo Logic
This is a newer, cloud-based platform appropriate for SMBs in terms of both cost and features. Since the product is new, there isn’t much of a community base in place, but Sumo Logic claims its product fills gaps in IT security that other products have missed—especially when it comes to cloud deployments. Note that this tool seems to have more of a technical user in mind, so the design features aren’t as appealing.
7. Datadog
© 2024 Datadog
Datadog is a log monitoring and analytics platform that has expanded into a comprehensive and robust security monitoring and SIEM tool. It offers real-time monitoring, anomaly detection, and integration with DevOps and IT workflows. Datadog’s strength is in cloud and application monitoring, which makes it great for collaboration between developer and security teams. It also has an intuitive and user-friendly interface that you can use to visualize your logs to gain insight. However, since Datadog focuses more on operational monitoring than traditional SIEM tools, additional tools may be required for comprehensive security coverage. Luckily, it has over 700 integrations that’ll help you gain visibility into your infrastructure.
8. FortiSIEM
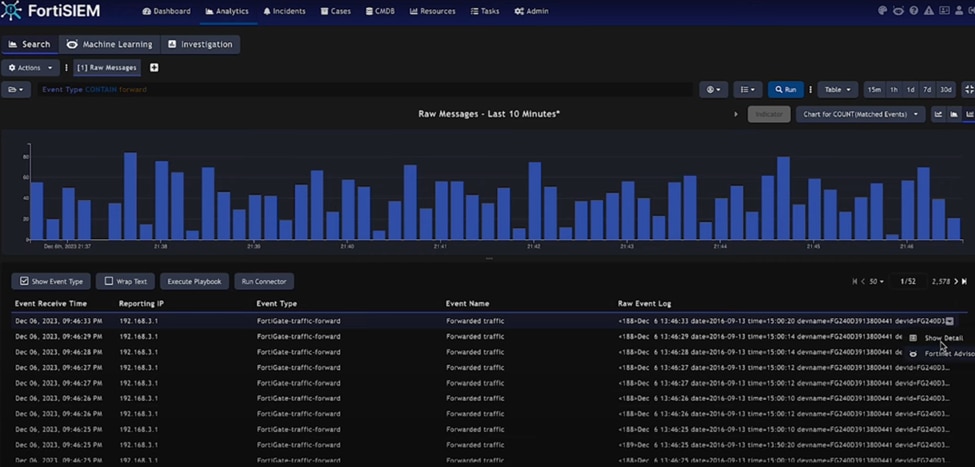
©2024 Fortinet
FortiSIEM is an integrated SIEM solution that is part of Fortinet’s security fabric. It’s the only tool with an inbuilt configuration management database (CMDB). It offers multi-tenant architecture, real-time threat detection, distributed real-time event correlation and automated compliance reports. FortiSIEM integration with other Fortinet products is scalable and supports both on-premises and cloud deployments. Unfortunately, it can have a complex pricing model.
9. Microsoft Azure Sentinel
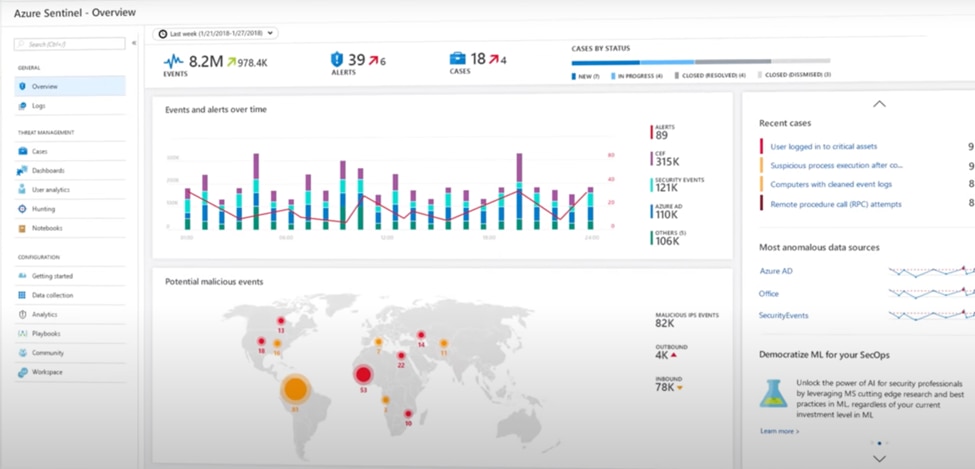
© 2024 Microsoft
Azure Sentinel is a cloud-native SIEM and SOAR solution provided by Microsoft. It offers intelligent security analytics and threat intelligence across the enterprise. It includes integrated SOAR capabilities and seamless integration with Microsoft products. Azure Sentinel is scalable, cost-effective for Azure customers, and has minimal infrastructure management. Since it’s primarily designed for Azure environments, it may have limitations for on-premises or multi-cloud setups.
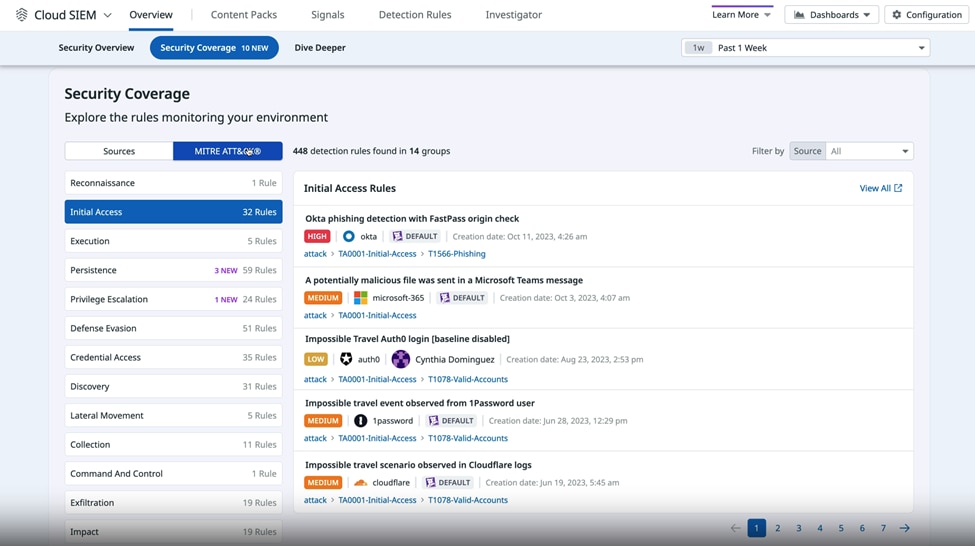
10. Securonix
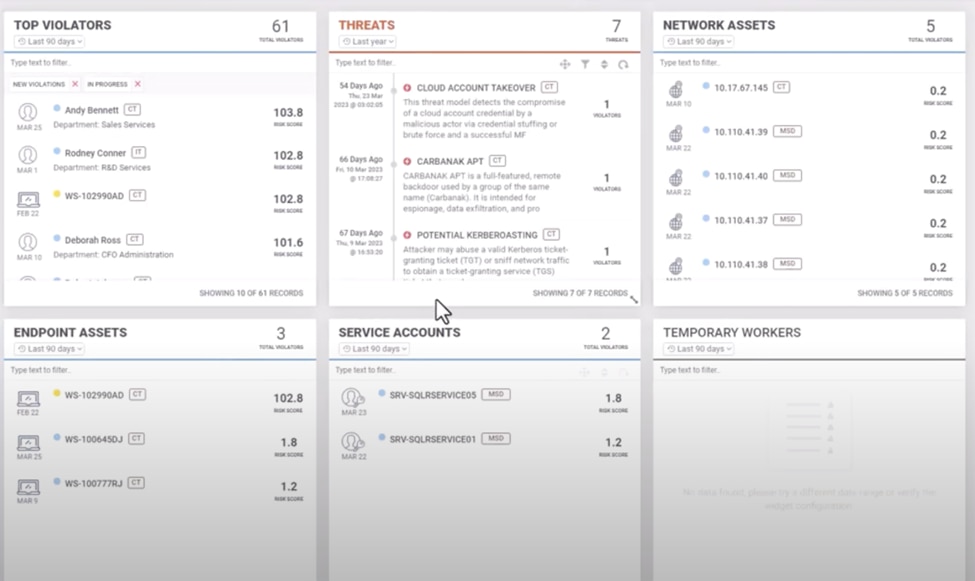
© 2024 Securonix
Securonix is a cloud-native SIEM platform that focuses strongly on behavior analytics. It has advanced UEBA, NexGen SIEM capabilities, and big data architecture. Securonix is highly scalable and can keep up with large data volumes. It also encourages knowledge sharing through a community of collaborators. It offers powerful analytics, is good at reducing false positives, and has flexible data storage to handle large volumes of data. However, it can be pricey for large data volumes.
11. LogPoint

© 2024Logpoint
LogPoint is a European SIEM vendor offering a unified SIEM and SOAR solution. Their SIEM tool includes machine learning-driven analytics, UEBA, and automated incident response. LogPoint’s SIEM tool offers compliance reporting and an intuitive interface, which is good for mid-sized enterprises. Despite being a niche player, it has a smaller community than some competitors.
12. ManageEngine Log360
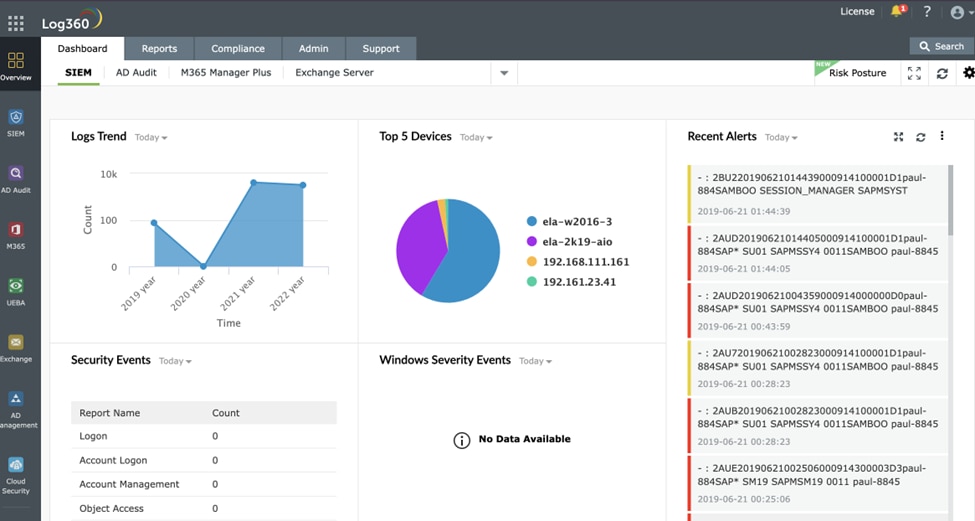
© 2024 ManageEngine.
ManageEngine Log360 is an integrated solution that combines SIEM, log management, and compliance reporting. It also has data loss protection (DLP) and Cloud Access Security Broker(CASB) features that identify and address threats. Log360 includes pre-built correlation rules, file integrity monitoring, and active directory auditing. It is easy to deploy and use, and with CASB, you get enhanced visibility and identity monitoring of users and applications in the cloud. Log360 is only available for Windows.
Read also: SIEM vs. Log Management
13. Graylog

© 2024 Graylog
Graylog is an open-source logging platform with advanced SIEM functionality. It includes log processing, management, and extensible functionality via plugins and custom dashboards. Graylog is adaptable, affordable, and has strong community support. However, it offers fewer features than commercial alternatives and requires technical expertise to set up.
14. Elastic Security
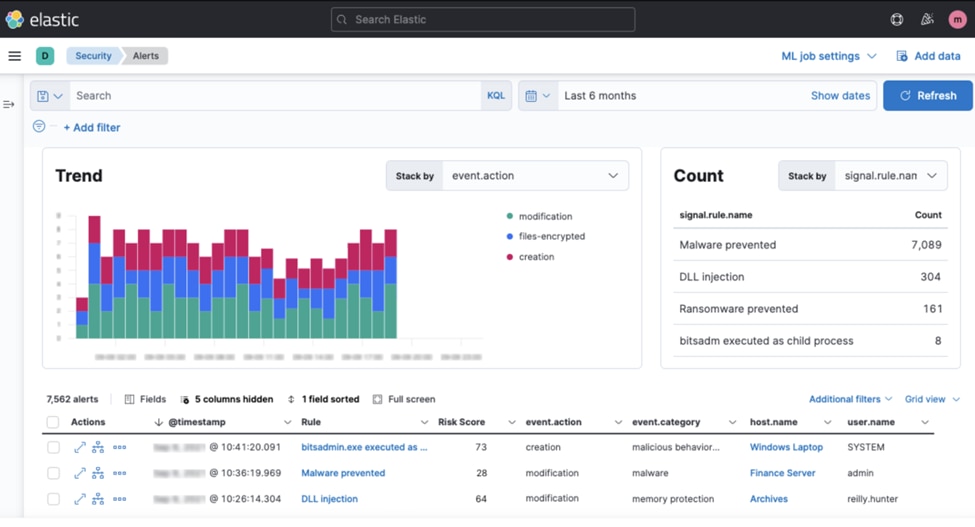
© 2024 Elastic
Elastic security is a SIEM solution built on the Elastic Stack that offers powerful search capabilities. It includes full-stack visibility, built-in case management, and endpoint security integration. Elastic security is highly scalable, flexible, and robust in log management and search. However, because of the complex setup and management, skilled personnel are required for effective use. It also has a steep learning curve.
15. Insight IDR
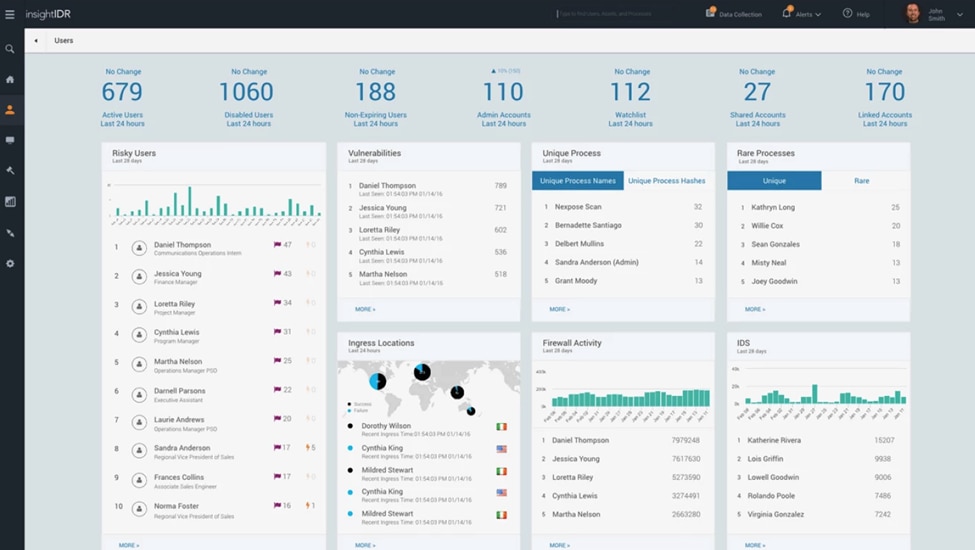
© 2024 Insight IDR
Insight IDR is a cloud-native SIEM solution focused on user behavior analytics and threat detection. Its key features include user and entity behavior analytics (UEBA), attacker behavior analytics, network traffic analysis, and cloud-based log management. Insight IDR offers an intuitive user interface and is strong in detecting compromised credentials and insider threats.
However, it requires additional tools for comprehensive security monitoring, primarily cloud-focused.
What to Look for in the Best SIEM Solutions
Every business will have its criteria for deciding whether a tool’s capabilities align with its needs when choosing a SIEM security solution. This will depend on factors like business size, types of data, vendor array, specific regulatory frameworks, budget, and, of course, an IT team’s usability preferences.
You should ask a few questions as you evaluate the best SIEM tools on the market.
- Will the tool improve your log collection abilities? This is basic but important, as you want software that enhances your ability to collect and manage logs. Look for compatibility across systems and devices; having a dashboard with user-friendly features never hurts.
- Will the tool allow you to achieve compliance? Look for a tool that helps with auditing and reporting. Even if you’re not concerned with compliance now, you should be. A SIEM tool is a great way to improve your game in this area.
- Is the threat response workflow set up to help you manage past security events? One major advantage of a SIEM tool is that it allows you to get an overview of past events, analyze what happened, and instruct the system to use historical patterns to inform its activity. Look for helpful, drill-down analytics capabilities.
- Does the tool provide the fast, effective, automated responses you need? First, it’s critical that incident response time is fast enough. Additionally, customizable security alerts can make your life easier. You want to turn away without wondering whether you’re neglecting a major issue. Make sure alerting is a priority within the tool.
If you ask these questions as you check out SIEM tools, you’ll be well-positioned to make a smart decision. The questions guide you on what to look for when consulting various SIEM vendors in the market.

Final Thoughts about best SIEM tools
If you’re looking for the best all-around security and log management option for Windows and Mac OS, look no further than SolarWinds SIEM tool Security Event Manager. It’s easy to use and features intuitive, appealing dashboards that let you centralize and streamline your operations without sacrificing in-depth insights. Don’t forget that you have a 30-day trial period to try it out and decide if it’s right for you!
Additional Resources:
Best Free and Open Source SIEM Tools
Free trials of enterprise-grade SIEM software are a great way to evaluate a solution and determine whether you need the features a full SIEM software can offer.
Best Server Monitoring Software
If you’re researching log management solutions, I wouldn’t be surprised if your company could also use a server monitoring upgrade. This post breaks down what server monitoring means today so you can stay on top of system resource usage — even in the era of cloud computing.
Log management is an important component of SIEM, but this is the list you need if you’re looking specifically for log data solutions. Get software stats about message-per-hour, storage, Windows events, and everything else that factors into this function.
