Microsoft OneDrive for Business is a cloud-based storage platform designed to help you organize, access, edit, update, and send files across devices. In 2014, Microsoft launched OneDrive, a rebranding of its original storage platform SkyDrive, with a mission to simplify cloud storage for all.
Many businesses choose OneDrive because it offers many opportunities to share and collaborate on a variety of files. This is especially the case for large companies with offices spanning countries and continents. According to Microsoft, over 85% of the Fortune 500 companies use OneDrive, including Lowe’s, Kraft Heinz, and Chevron.

Improving Efficiency With OneDrive for Business
Microsoft offers several OneDrive for Business plans to fit the price point of any enterprise. You can start as low as $5 per user per month or go as high as $35 per user per month. With greater spend comes greater storage capacity, detailed analytics, and video conferencing capabilities, among other perks. A few of the functions you can expect across all plans include:
- Remote Opportunities: OneDrive allows you to easily access your files from any device (laptop, tablet, mobile, etc.). You can even choose to download specific files you want to access or edit offline. This capability can help you capitalize on formerly unproductive periods—like long subway commutes—and turn them into efficient work opportunities. Any edits you make offline are automatically updated as soon as you regain connection.
- Enhanced Mobile Functionality: The OneDrive app for iOS and Android are particularly user-friendly and further make the case for remote capabilities. You can also use the app to scan, save, and upload receipts, contracts, invoices, and other critical documents. Gone are the days of being tied to a large, traditional scanner.
- Collaboration Capabilities: Owners of a file can simultaneously edit and review a document, making it faster and easier to gather feedback. OneDrive also makes it convenient to share files across teams and organizations via links. You can set restrictions for each—view-only or edit—as well as expiration dates.
- Expanded File Forms: OneDrive works seamlessly with all Office 365 applications (Word, PowerPoint, etc.) and allows you to review and edit over 300 file types, from documents, spreadsheets, and presentations to X-rays and 3D files.
A perfect example of OneDrive in action is the creation of a presentation deck. If you’re a Chicago-based organization with offices in Raleigh and San Francisco, you can draft an outline of the presentation in PowerPoint, then share this and any supporting files with your marketing agency in New York via the OneDrive link function. Once you have the designed copy in hand, you can ask your team across offices to provide feedback. Members can edit and comment on the same document at once, no matter where they’re located. OneDrive boosts efficiency and makes it easier to get projects done more quickly.
OneDrive Security Best Practices
OneDrive is designed to be secure at the enterprise level. OneDrive prides itself on its commitment to the “core tenets of earning and maintaining trust: security, privacy, compliance, and transparency.” In line with this commitment, OneDrive has implemented data encryption technologies, adjustable access and sharing capabilities, and sensitive data classification opportunities. An example of these practices in play is the ability to send files with a one-time verification code. This code is emailed to the recipient upon access attempt and provides a second layer of security.
Despite these efforts, many IT teams are wary of storage platforms and their ability to keep company files safe and secure. A survey of U.S. IT and security professionals conducted by the Cloud Security Alliance found that more than 50% believe cloud storage is the riskiest cloud app category. Of those surveyed, 68.1% said they have security policies and procedures in place to ensure data security and compliance in cloud apps.
Their worry isn’t unwarranted. When a breach occurs, highly sensitive data, non-public financials, customer data, and employee records could all be compromised. Simply put, there’s a lot at stake. Many of the OneDrive for Business security concerns out there include:
- OneDrive Secure File Sharing: The ability to upload and share files with users outside of the company can be risky. Having policies in place to help limit the spread of sensitive information should be a critical part of any IT team’s security strategy.
- Device Compatibility: Many companies allow employees to access their cloud network on personal devices, like cellphones and laptops. The more devices that have access to OneDrive, the greater the chances a device is lost or, worse, stolen. A device in the wrong hands could lead to a data breach. If companies are going to permit employees to use their own devices, they also must have ways to monitor those devices.
- Violations of Trust: Verizon’s 2018 Data Breach Investigations Report found that 28% of security attacks involved individuals with legitimate access to company data. While it’s important to trust your employees, it’s equally important to monitor the activity surrounding sensitive files and stay aware of suspicious behavior.
- Inappropriate Permissions: Not all employees need access to every file within your database. When you open up privileged accounts to those beyond the necessary individuals, you’re increasing the chances of a virus. Be sure to set appropriately hierarchical permissions levels.
- Delayed Response: Thousands of files and folders can be stored within the cloud storage system and accessed by equally as many users. This makes it difficult to know exactly when corruption occurs and can delay appropriate response measures. The Verizon report indicates that 68% of breaches took months or longer to discover.
- User Credentials: Credential theft and misuse is one of the most common tactics used by cyber attackers. That’s because these credentials are stored on the cloud itself and, depending on the user, can range greatly in their level of security. It’s important to have a password policy in place to ensure all your employees are following password best practices. Once an attacker gets his or her hands on a user’s credentials, they can navigate their way into the cloud and gain access to sensitive data.
Tools for Ensuring OneDrive Security
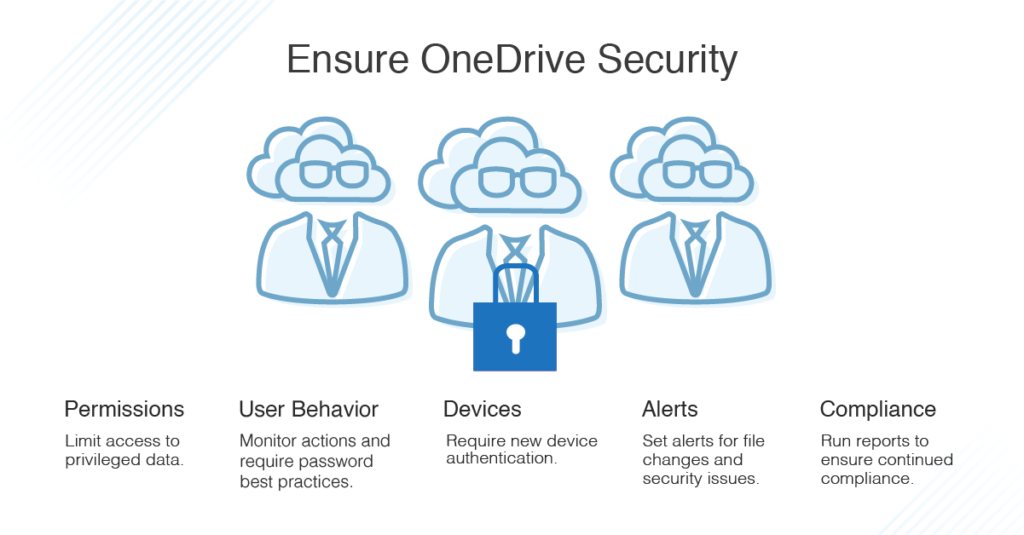
There’s hope for IT teams looking to avoid OneDrive security risks and go above and beyond the security measures offered by the cloud storage platform. Access management tools have entered the industry to provide IT and security professionals with a complete overview of their cloud storage and sharing platform and protect their organization’s data. Here are a few of the ways an access rights manager can help you:
- Monitor OneDrive Permissions: Access rights management software can come equipped with detailed—yet intuitive—dashboards that provide a bird’s-eye view of each user’s access to services and file servers.
- Analyze User Behavior: Gathering information on user behavior allows you to verify policy compliance and better secure user credentials and data. It also ensures you have the necessary data on hand to support an investigation if a security issue does occur. With an access rights manager, you can monitor changes to mailboxes, folders, and calendars.
- Act Quickly: IT teams have 24 hours following a cyberattack to act before recovering any lost data becomes an unlikely outcome. An access rights manager will trigger alerts when suspicious activity—such as unauthorized access—occurs so you can take action before the damage is done.
- Automate User Accounts: Management tools remove the tedious side of IT operations by automating access management. With role-specific templates, standardized, secure account creation is easy. This streamlines user onboarding and enables a quick response to user account termination requests. What if a threat is detected? These tools will automatically deprovision the suspicious account.
- Protect Credentials: Being proactive is the best way to protect against security breaches. Access rights managers will immediately identify if a user account has insecure configurations to help protect you against credential theft and misuse of authorization and access.
- Remain Compliant: Auditors assess HIPAA and/or PCI compliance and will look to see if user management policies are being monitored and enforced. Access rights managers can generate custom reports that show which employees have access to what documents. They also offer historical data, so you can view when a file was accessed. Some platforms take all this a step further, offering scheduling capabilities that allow you to automatically generate and send reports to auditors on a timeline of your choosing.
Backup Key Data: No matter how careful you are, there’s always the chance for important data to become lost, stolen, or corrupted. In those scenarios, you need to have reliable backups stored in an easy-to-access location. For MSPs in particular, N-able Backup is the perfect solution. It streamlines and simplifies the backup process, giving you backup options, storage access, and multiple recovery tools all in the same convenient dashboard. It’s fully compatible with OneDrive as well as other platforms, such as Microsoft Exchange and SharePoint.
Making Protection a Priority
A security breach can cause serious financial and reputational damage to a company of any size. While over a quarter of security attacks involved insiders, as we mentioned, almost three-quarters were conducted by outsiders, with members of organized criminal groups behind half of these episodes. IT and security professionals must take every possible measure to ensure their data is protected—within the company and beyond.
But that doesn’t mean you shouldn’t use a cloud storage system like OneDrive. Security and convenience can go together. Access rights management tools bring a plethora of easy-to-implement security capabilities right to your fingertips. With user analytics, automated user account provisioning and deprovisioning, comprehensive compliance reports and more you can easily maintain control over your company’s most viable assets while using a cloud storage solution.
