OpenTelemetry Overview: Unifying Traces, Metrics, and Logs
The IT landscape has evolved rapidly, transitioning from monolithic applications to complex, distributed system architectures comprising microservices that run on platforms like Kubernetes. With this added complexity, simply checking if a server is running is no longer sufficient. As IT professionals, we need insight into what’s really happening inside these systems. That’s where observability comes in. This is where…
The Ultimate Guide to Kafka Monitoring Best Practices, Metrics, and Tools
If you’re operating modern, data-driven applications—which, let’s face it, you likely are—Kafka serves as the central streaming platform, delivering data in real-time. It’s impressive, extremely fast, and exceptionally powerful for achieving high throughput and scalability. But here’s the catch: with significant power comes the need for vigilant oversight. Neglecting your Kafka environment is like driving…
Application Performance Monitoring Guide: Strategies, Best Practices, and Tools
With the introduction of cloud services and microservices, applications have become more complicated due to their increased layers of complexity and distributed architecture. While microservices clearly offer speed, they also make things harder for the developers and operations teams. These teams need to plan for the reliable and efficient performance of such applications. To combat…
How to Tame and Redefine Your Network Now
The network as we know it is being redefined. As more endpoints, applications, and devices are added to the mix, the network is transforming. For IT, the challenge is two-fold: stay on top of the network today, and prepare for what it could look like tomorrow. In an environment where workers expect to be online…
Best System Monitoring Software
IT teams know the stakes are high for system monitoring. It’s not an overstatement to say tracking the health, performance, and security of the many IT components throughout your environment is crucial if you hope to ensure the overall organization stays operational and secure. When businesses don’t invest in the right solutions for measuring system…
How to Open and Check Server Log Files
Wondering how to check logs from your servers, and why? Whether web servers, application servers, file servers, or another type, your servers constantly generate log files based on activities and events, and your ability to review these files is the key to fast, effective troubleshooting. Server log files offer “behind the scenes” views into server…
Syslog Monitoring Guide + Best Syslog Monitors and Viewers
Syslog is a network-based logging standard used for applications to send data to a central server, providing information on events, statuses, diagnostics, and more. Unlike SNMP, which is an active approach to monitoring (aimed at preventing the occurrence of incidents), Syslog monitoring provides a passive approach, which allows you to deal with incidents after they…
How to Access Linux Desktops From Windows Remotely
Whether you need to allow employees to efficiently work from home or branch offices, or you want to facilitate troubleshooting tasks for the IT team, remote access is critical. For many IT support workers, providing remote support to users and remotely accessing devices has become an everyday necessity. Remote desktop connection for Linux systems from Windows machines…
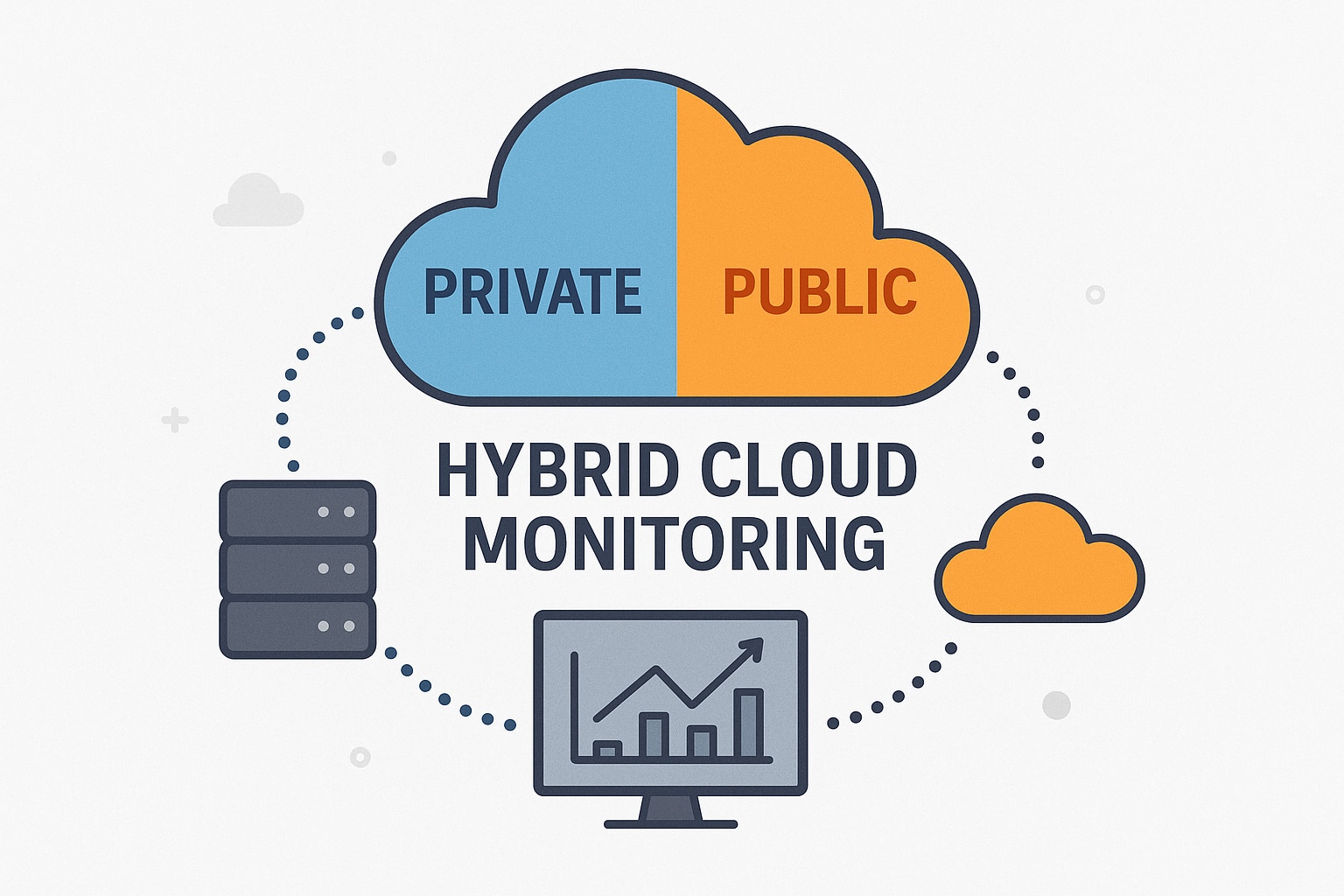
Hybrid Cloud Monitoring: A Comprehensive Guide to Strategies, Best Practices, and Tools
Modern infrastructures are no longer confined to on-premises servers alone. Instead, they span cloud environments, containers, microservices, and globally distributed systems. This landscape, known as a hybrid cloud environment, has become the new norm for organizations, primarily because it offers the scalability of the cloud and ownership over specific elements afforded by an on-premises setup….
What Is Infrastructure Monitoring? – 6 Best Software for Infrastructure Monitoring
Infrastructure monitoring is the continuous and systematic observation of infrastructure components that collect and analyze an organization’s data, ensuring efficient and reliable operations. What is infrastructure monitoring? How Does Infrastructure Monitoring Work? Infrastructure monitoring for cloud environments Methods of Collecting Data for Monitoring Infrastructure Monitoring Use Cases What Are the Best Practices for Infrastructure Monitoring?…
Best Application Performance Management Tools and Software
Application performance management is the process of managing and monitoring applications to ensure they’re behaving normally and aren’t impacting service levels. Ensuring good application performance keeps your end users happy and prevents low-quality experiences like slow applications or bugs. Using a professional application performance tool is critical to managing your systems and ensuring all your…
Best Application Monitoring Tools
As monitoring aficionados, our toolbox sports an embarrassment of riches, from configuration management to logging, and from synthetic transaction solutions to application tracing and monitoring. It could be argued that cloud-based application monitoring (or APM) tools are the most plentiful and, to a certain community of IT practitioners, the most essential, providing crucial information to…
Best Server Monitoring Software
Once upon a time, “server monitoring” was a delightfully straightforward category of the monitoring sub-discipline within IT. There was a box, the box had an operating system, and that operating system did certain things for the organization. Even when the word server became conflated to mean both “the box in the data center” and “the…
SSL Certificate—How to Monitor and Manage Certificates
Maintaining data security is a top priority for any organization. Secure Sockets Layer certificates—usually called SSL certificates—are an important part of this effort. SSL certificates are small data files designed to prevent hackers from getting access to private business data as it passes between a website and a visitor’s browser. They do this by creating…
Best Free Log Management Tools
The log management tools I feature here are either free or have a free tier of service. While it’s fantastic to find a bargain, that doesn’t always make it the best choice for a given use case. IT budgets aren’t infinite, I get that. But don’t let budget considerations alone keep you trapped in log…
Best NTFS Permissions Reporting Tools in 2020
For most IT teams, selecting the right permissions reporting tools is a high priority. Understanding access rights across an organization’s network is crucial when striving to protect sensitive or confidential information and having proof of permissions management is a fundamental tenet of compliance with internal controls regulations.
Best Solutions for Business File Sharing
With the spread of remote work and contractual employees, business file sharing has never been more important. The right software solution needs to handle massive file sizes without a hitch, but it also needs to be optimized for secure file sharing. Fortunately, there are a number of great solutions on the market, so much so…
15 Top Log Management Tools in 2024
With the three pillars of observability considered more or less canon for IT monitoring philosophy these days, and logging being one of those pillars, it’s important to understand the tools, systems, and solutions that help IT practitioners do a good job of aggregating, normalizing, and leveraging logs in all their forms to provide improved insight…
Common Database Problems and Performance Issues
There are few things more important in your IT infrastructure than database performance. DB performance metrics can be easily tracked, and there’s no excuse for not doing so. There are several common database problems you’re likely to encounter when managing a large IT network, and solving these quickly can make a big difference in terms…
SQL Performance Testing Tools for Servers—What You Need for Stress Tests
SQL Server performance testing is an invaluable practice and can yield notable benefits. SQL Server performance tests can be used for a range of purposes, included but not limited to performance tuning, capacity planning, and identifying bottlenecks. This article will outline the importance of SQL performance testing, what you need to get started with stress…
Top Database Management Systems
Databases are the collective sources of an enterprise’s information stored on a dedicated server or in the cloud. A database management system (DBMS) is software that stores, retrieves, and updates this data, manipulating the database, so it can be used effectively by many people at the same time. These are referred to as relational database…