How to Tame and Redefine Your Network Now
The network as we know it is being redefined. As more endpoints, applications, and devices are added to the mix, the network is transforming. For IT, the challenge is two-fold: stay on top of the network today, and prepare for what it could look like tomorrow. In an environment where workers expect to be online…
The Evolution of the Web and Digital Experience Monitoring
Digital Experience Monitoring (DEM) is so business critical that it’s featured in a Gartner magic quadrant. At the same time, it is so new that even Wikipedia does not know what it is. (related read: What is Digital Experience Monitoring (and Why Should You Care)? Why is that? Monitoring as a practice is as old as dirt,…
Why Cloud Is Best For Log Management
Log data is the currency for companies trying to evolve in today’s digital world. To meet increasing customer demands, critical compliance requirements, and scaling application needs, it’s essential to collect and leverage massive data flowing across multiple sources and environments (cloud, on-premises, containers, etc.). Log analysis gives you valuable insights into business-critical events, real user…
What Is Digital Experience Monitoring and Why it Matters
Today, businesses are investing heavily in digital technologies to improve different aspects of their business and get an edge over the competition. Customers are at the center of most of these digital initiatives, and businesses are always seeking better tools and systems to track customers and understand their needs. Businesses need to understand how their…
What Is Cloud Monitoring? A Guide Through the Best Tools
As more businesses embrace digital transformation, cloud computing is becoming more relevant each day. Cloud technology provides the flexibility, scalability, and agility modern organizations need to stay competitive, transforming everything from daily operations to customer experiences. However, as companies expand their use of the cloud, managing these complex environments is proving to be a real…
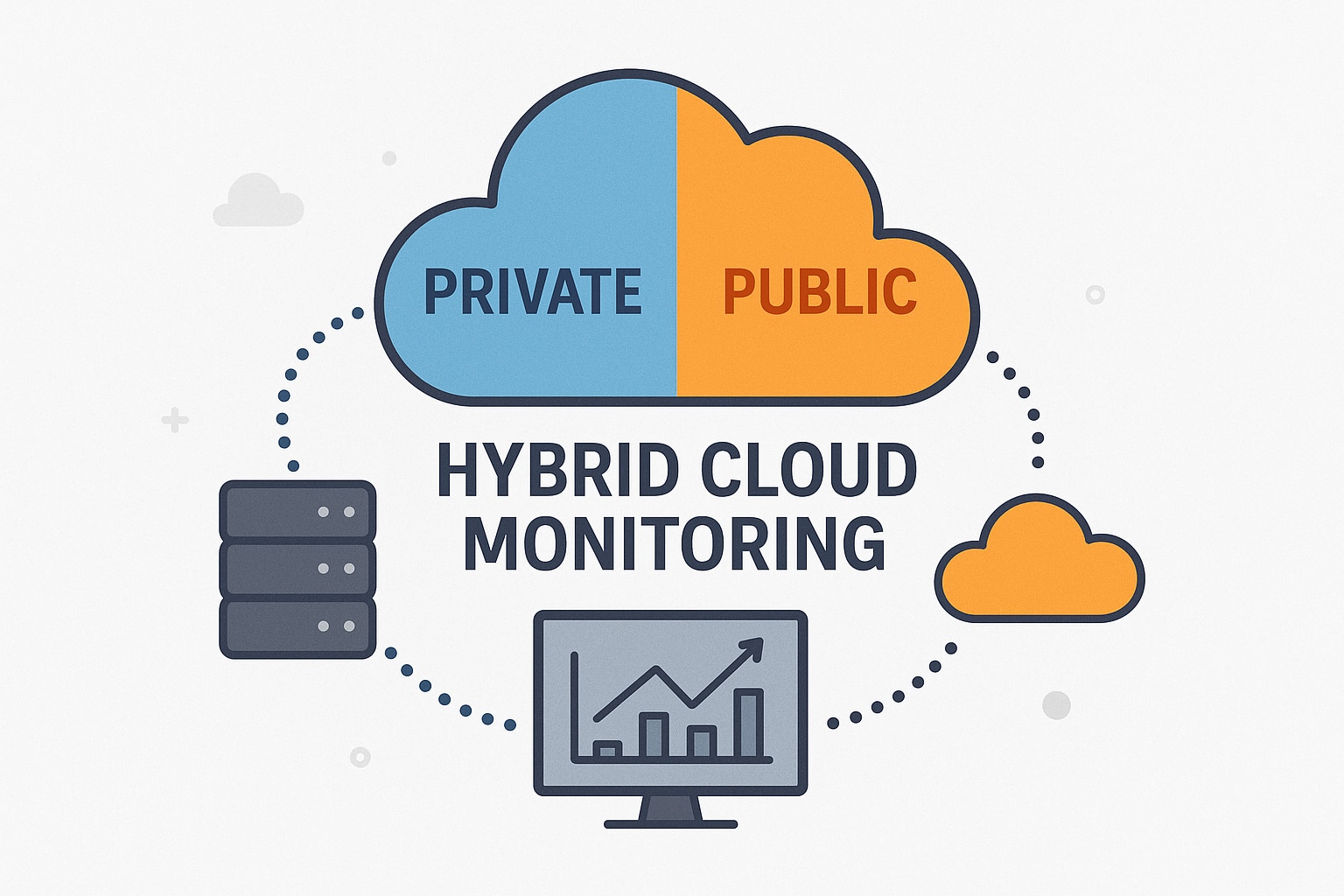
Hybrid Cloud Monitoring: A Comprehensive Guide to Strategies, Best Practices, and Tools
Modern infrastructures are no longer confined to on-premises servers alone. Instead, they span cloud environments, containers, microservices, and globally distributed systems. This landscape, known as a hybrid cloud environment, has become the new norm for organizations, primarily because it offers the scalability of the cloud and ownership over specific elements afforded by an on-premises setup….
Top Monitoring and Optimization Tools for Docker
Docker is a multipurpose tool that can replicate many functions of a virtual machine with less of the hassle. Because Docker operates using virtual software packages (called “containers”) running from the same software kernel, Docker can help you reduce storage overhead while deepening the complex functions of your server. Using Docker can instantly allow for…
5 Best Practices for Container Monitoring
Best Practices Software and infrastructure monitoring is a must in any modern environment. Monitoring not only helps you spot issues and bugs, but done correctly, it can help you optimize your software’s performance. The actual implementation, however, will differ depending on your infrastructure. For example, monitoring containerized applications requires a slightly different approach than your…
How to Tail Kubernetes (and kubectl) Logs
So, you have a Kubernetes cluster. Let’s make sure you know how to see what’s going on inside. In this blog post, you’ll learn how to review logs from Kubernetes and what you may want to be running in it. Start by Looking at the System The first thing you may want to look at…
Top 7 Kubernetes Add-ons
The open-source Kubernetes platform is designed to help simplify application deployment through Linux containers. It supports tasks like deploying workloads in the form of pods, clustering nodes, managing container runtimes, and tracking resources. The Kubernetes microservices system has risen in popularity over the last several years as an easy way to support, scale, and manage…
Understanding Kubernetes Performance: Top Tips From Experts
What’s Important for Kubernetes Performance The way Kubernetes works “under the hood” dictates which components are more important for improving performance and which are less important. So let’s talk about the Kubernetes internals first. Kubernetes Internals The most important thing you need to know about Kubernetes is it follows “hub-spoke” architecture. We have a control-plane…
Java Application Performance Monitoring: Eight Tips and Best Practices
Java is one of the most popular programming languages. It’s powerful yet approachable, allowing both new and experienced developers to work with it in an efficient manner. And thanks to the Java Virtual Machine (JVM), Java is deployable regardless of operating system and architecture, which lowers the cost of adoption and makes it a versatile…
Best Application Monitoring Tools
As monitoring aficionados, our toolbox sports an embarrassment of riches, from configuration management to logging, and from synthetic transaction solutions to application tracing and monitoring. It could be argued that cloud-based application monitoring (or APM) tools are the most plentiful and, to a certain community of IT practitioners, the most essential, providing crucial information to…
Comprehensive Guide to Log Aggregation Techniques and Tools
Logs can provide vital insights to help you monitor system health, pinpoint and resolve issues, and improve cybersecurity. They capture real-time errors and record information about events and other system activities, shedding light on everything from application performance to security threats. However, managing logs can be overwhelming. To get the most out of your logs,…
Dameware Products Review and FAQs
Remote access solutions are incredibly common in enterprise and large business setups, as administrators can quickly and easily resolve support issues or go through troubleshooting without needing to be physically present at the device. There are several remote access software options on the market, and SolarWinds® Dameware® provides three options to accommodate the full range…
Best Free Log Management Tools
The log management tools I feature here are either free or have a free tier of service. While it’s fantastic to find a bargain, that doesn’t always make it the best choice for a given use case. IT budgets aren’t infinite, I get that. But don’t let budget considerations alone keep you trapped in log…
Guide to Data Observability
The way we manage, qualify, and utilize our data is constantly tested. With the amount of information we have at our disposal, managing and ensuring data quality has become a strategic lever for companies striving for excellence. How can we ensure our data management is flawless and the data quality on which we base our…
Quick Guide to Searching and Filtering JavaScript Logs
It can be messy—and oftentimes overwhelming—when your log prints piles of errors or warnings. As you execute programs with front-end languages like JavaScript, your web console keeps log entries. You can access log entries from your web console with browsers such as Firefox, Google Chrome, etc. Logging simply involves keeping track of all the changes…
IIS Log Analysis – Best Tools and Practices
When you host applications on Microsoft web server technology Internet Information Services (IIS), your system administrators must carry out the ongoing task of IIS log analysis. This means they monitor the variables indicating whether IIS-hosted applications are running at optimal performance. You can also use IIS logs to check the security and integrity of said…
What Is a DDoS Attack and How Can You Detect It With Log Analysis?
Businesses are moving their entire infrastructure to the cloud due to its incredible virtual services, proactive support, and better scalability. However, with increased exposure to the internet and cloud, organizations’ threat surface also increases significantly. A DDoS attack is one of the most common cyber threats affecting business productivity and connectivity across the globe. Recent…
How to Monitor Your Logs: Best Practices and Top Log Monitoring Software
In the last decade, IT infrastructure has evolved significantly. From small startups to established enterprises, everyone has gradually shifted their systems, data, and applications to the cloud. However, this transition is far from over; the tools and technologies for application delivery via containers, microservices, serverless, and other cloud-native technologies are still going through a refinement…