Reduce PHI Risk Exposure With a Strategy That Supports HIPAA Compliance
Health Insurance Portability and Accountability Act (HIPAA) compliance is about more than firewalls and passwords. Your file-sharing solutions could be the weakest link in protecting sensitive patient data. When we think about healthcare cybersecurity, we tend to focus on large systems: electronic health records, databases, and billing platforms. But one everyday workflow that’s also as…
How to Set Up a Syslog Server: A Complete Step-By-Step Guide
Syslog servers are essential for centralized log management, helping network engineers monitor, troubleshoot, and secure network devices efficiently. This guide walks you through setting up a syslog server from scratch, focusing on practical steps using rsyslog on a Linux system – a common and robust choice for syslog collection. Windows does not have a native…
Cloud Cost Optimization Best Practices, Strategies, and Tools to Reduce Bills
As network engineers, you play a crucial role in managing cloud infrastructure that supports your organization’s applications and services. Cloud platforms offer immense flexibility and scalability, but without careful cost management, expenses can quickly spiral out of control. This article provides a comprehensive guide to cloud cost optimization tailored for network engineers, focusing on practical…
Serverless vs. Containers: A Comprehensive Guide to Choosing the Right Solution
In the rapidly evolving world of cloud computing, network engineers often need to decide between serverless computing and containerization. Both technologies offer unique advantages and are suited to different types of applications. This article aims to provide a comprehensive comparison of serverless computing and containers, helping network engineers make an informed decision based on their…
Kubernetes CPU Limit: How to Set and Optimize Usage
Kubernetes makes it easy to scale applications. But when it comes to CPU resource management, a poorly tuned cluster can quickly become unstable or inefficient. For network engineers, setting CPU requests and limits correctly, and understanding the deeper implications, is essential for keeping workloads efficient, costs predictable, and noisy neighbors in check. What Are Kubernetes…
5 PCI DSS File Transfer Requirements You Can Meet With Serv-U
Compliance with the Payment Card Industry Data Security Standard (PCI DSS) is essential for any organization that handles credit card data, and it extends far beyond databases and payment gateways. One area often overlooked is file transfer workflows, which can pose serious risks if not properly secured. Whether you’re transmitting reports, sharing files with vendors,…
2025 Buyer’s Guide – Choosing Unified Infrastructure Monitoring
Unified infrastructure monitoring delivers a single, enterprise-grade platform to oversee hybrid environments, providing real-time insights and proactive health monitoring across on-premises, cloud, and edge systems. As 2025 brings new challenges with artificial intelligence (AI), edge computing, and hybrid complexity, SolarWinds stands out as a thought leader in unified infrastructure monitoring for enterprises. In this guide,…
How to Tame and Redefine Your Network Now
The network as we know it is being redefined. As more endpoints, applications, and devices are added to the mix, the network is transforming. For IT, the challenge is two-fold: stay on top of the network today, and prepare for what it could look like tomorrow. In an environment where workers expect to be online…
15 Best Change Management Software for 2024
What is change management software, and how does it help you deal with change, increase productivity, and foster a culture of adaptation for lasting success? How to choose the one that is best for your needs? Below we answer these questions and present the 15 best change management tools currently available on the market, which…
Differences Between RemotePC Attended Access and Dameware Attended Access
In today’s interconnected world, remote support solutions are essential for businesses and IT teams to assist users effectively. Among these solutions, RemotePC and SolarWinds® Dameware® are leading tools offering attended access capabilities. However, choosing the right tool requires thoroughly understanding its unique features, advantages, and ideal use cases. This article provides an in-depth comparison of…
The Ultimate Guide to the Best SFTP Servers in 2025
Secure File Transfer Protocol (SFTP), also known as SSH File Transfer Protocol, is a robust, encrypted method for transferring files across networks, designed as a more secure alternative to traditional File Transfer Protocol (FTP). Essential for industries handling sensitive data—like finance and healthcare—SFTP protects against unauthorized access and enables efficient file management, making it a…
Best FREE Syslog Servers
Every minute, your routers, switches, printers, firewalls, and more are sending syslog messages regarding their activity and overall functioning. To collect—and make sense—of these messages requires the use of a syslog server. With so many syslog servers on the market, finding the right one for your IT team depends on the size of your company,…
Best Syslog Servers in 2024
Logging is a critically important part of managing an IT environment, as it helps you spot issues with the system and reveal problems. Syslog is a kind of messaging protocol devices use to send messages about their status, events, or diagnostic information that can help with errors and troubleshooting.
Wi-Fi Bandwidth—Test and Monitor Bandwidth (And Three Recommended Tools)
IT admins know the importance of wireless network bandwidth when it comes to maintaining network performance. After all, if you have too many high-energy devices and applications putting a strain on your Wi-Fi or WLAN bandwidth, both your network performance and your end-user experience will suffer. How do you identify those bandwidth hogs, and how…
Wi-Fi Management – Recommended Software for Business and Guide
Many businesses rely on Wi-Fi for business productivity, particularly with the rise of BYOD policies. But if too many devices use an under-resourced Wi-Fi network, productivity can quickly slow to a halt. Wi-Fi management software offers a solution, by offering an automated way to monitor and analyze Wi-Fi devices, traffic, and other relevant Wi-Fi activity….
Best Network Traffic Generator and Simulator Stress Test Tools
Benchmarking the environment of a new network is a crucial part of ensuring its success when it goes live. This includes stress testing and generating traffic on existing networks, both of which help you to identify any potentially flawed or vulnerable areas—for example, drops in connection and packet loss. As we know, network traffic is…
Real-time Monitoring – Guide to Real-time Network Monitoring
Maintaining a reliable and secure network is essential for businesses of all sizes. Real-time network monitoring has become crucial, allowing organizations to monitor their network performance and security at every moment. This guide will explore what real-time monitoring entails, how it works, and why it matters for your organization. We will also look into some…
12 Best SNMP Monitoring Tools + Complete SNMP Guide
SNMP, short for Simple Network Management Protocol, is a widely used protocol and an essential piece of any network management strategy. IT administrators use SNMP monitoring to detect and manage devices, gain insights into performance and availability, and ensure the health of their network. In this guide, I’ll break down everything you need to know…
Best CPU Monitor Software and CPU Usage Programs
The central processing unit (CPU) is the core component of any device on a network, and it has the potential to dramatically affect the performance and stability of the network. When it comes to network management, effective CPU usage monitoring could be the difference between network stability and network performance deterioration. A powerful and dependable…
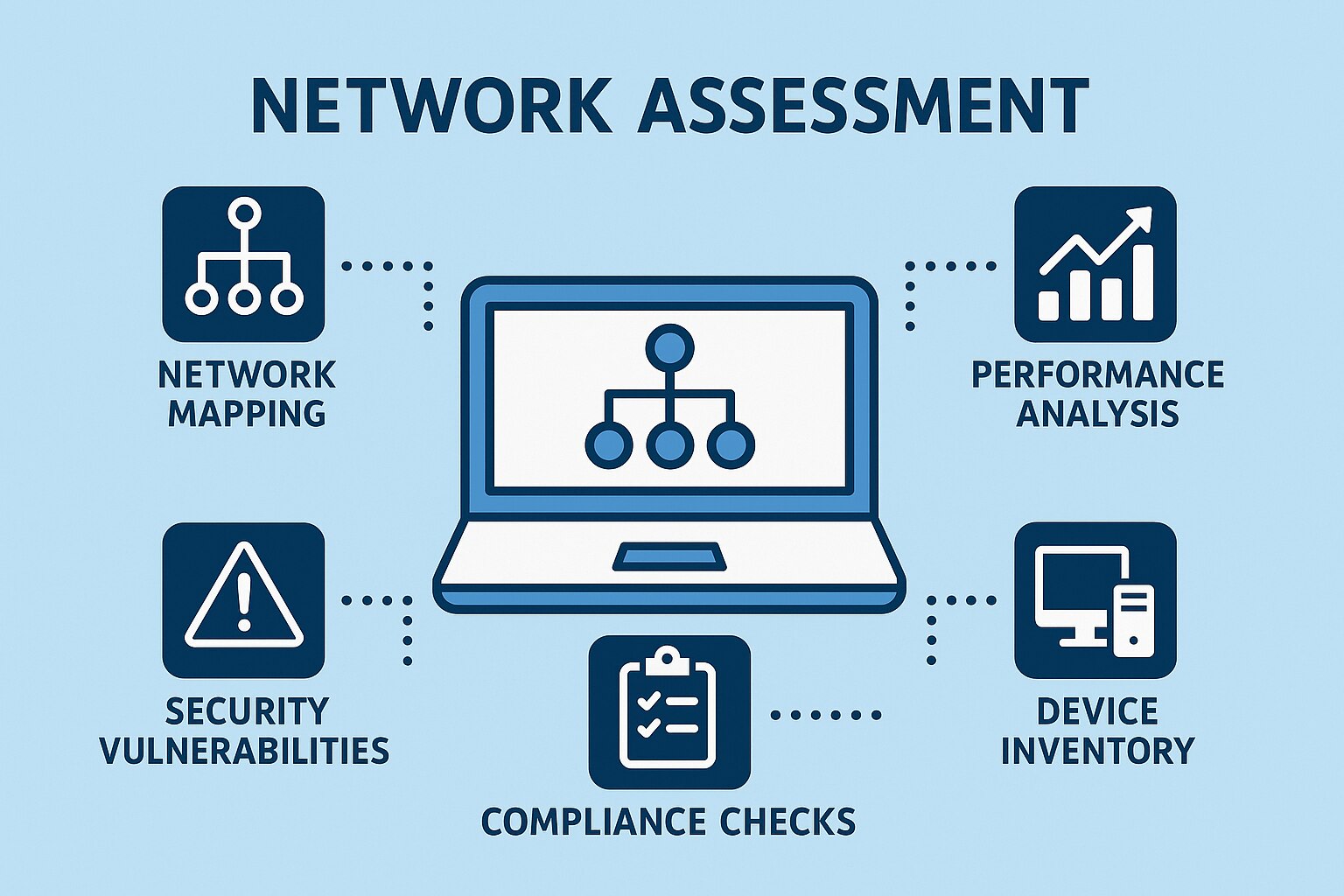
What Is a Network Assessment, and What Is a Network Audit?
These days, networks are larger and more complex than ever. It’s all too easy to fall short when managing performance, security, and compliance. That’s where network assessments and network audits can help. Both network assessments and network audits can give you a more comprehensive understanding of your network and its current strengths, weaknesses, and threats….
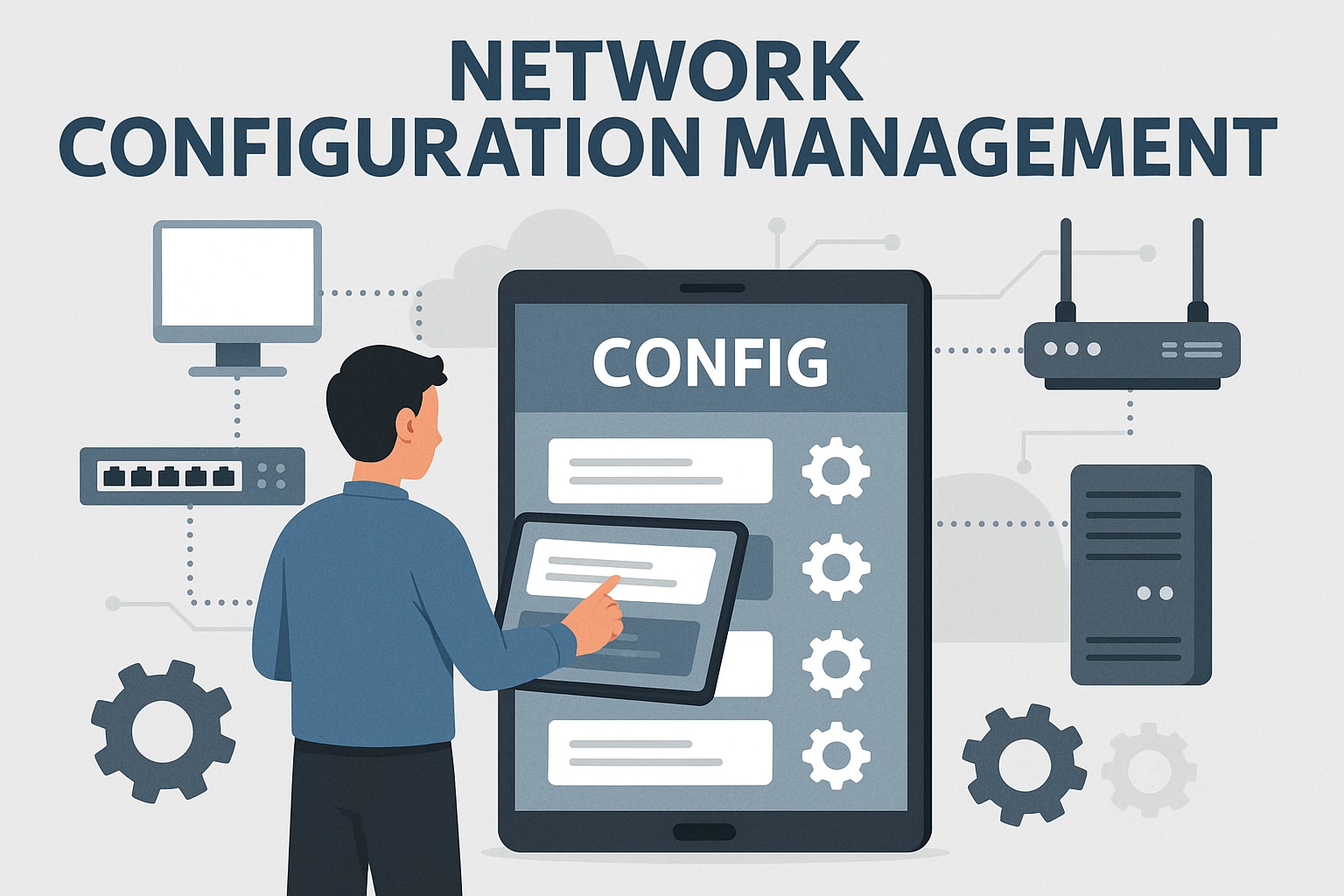
7 Best Network Configuration Management Tools
If you want a secure, efficient, and compliant network, network configuration management is a must. Whether managing a small network or being responsible for a large enterprise system, having the right solution can make all the difference. Network configuration management tools provide valuable insights into devices on your network, and they can help quickly restore…