From keeping track of IT inventory to handling help desk tickets on a daily basis, IT service management (ITSM) has become a mission-critical aspect of operating a successful and growing organization. Accordingly, businesses and other organizations have to be sure they’re giving their IT teams the tools they need to effectively respond to help desk requests, manage potential issues, and enjoy end-to-end visibility over their digital environment.
Although the right ITSM platform for your business is going to vary depending on your unique needs, there are some important features I think you should have on your wish list. For example, the best ITSM tools should help IT professionals manage tickets, ensure you’re in compliance with your SLAs, track inventory, and even stay on top of project management tasks. Ideally, your platform will offer automated functionality and an intuitive dashboard to get your IT team to the root of problems quickly without having to deal with an unwieldy or unhelpful user interface.
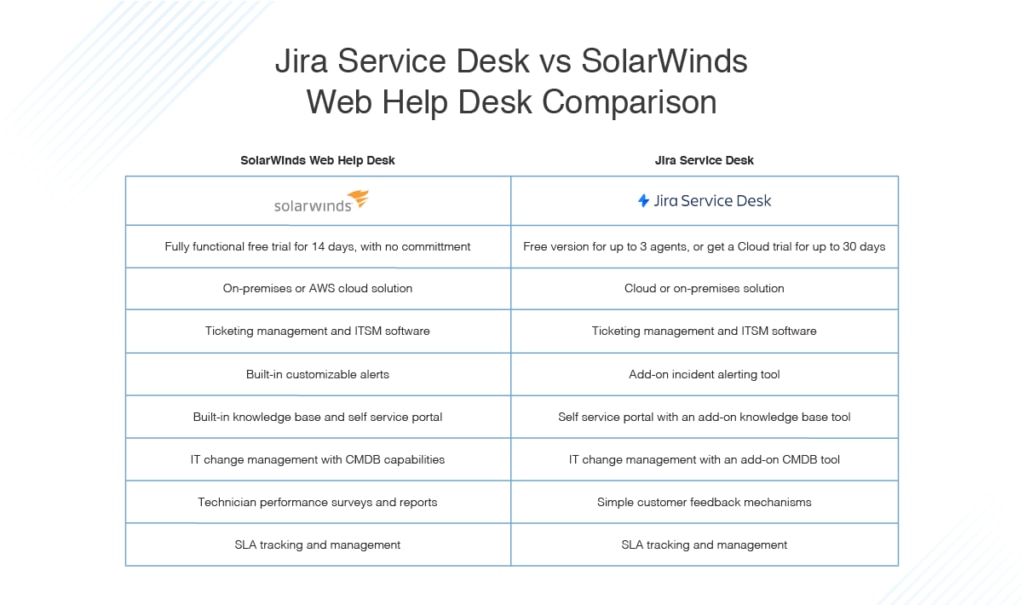
Two of the most popular ITSM platforms on the market today are Jira Service Desk and SolarWinds Web Help Desk (WHD). Both tools offer must-haves from every organization’s wish list, but also offer particular features that may be more appropriate for some business needs than for others. If you’re choosing between these products, I think you’ll find SolarWinds WHD offers a broader, stronger array of useful features. That being said, Jira Service Desk is a solid tool for the job and worth looking into if it has features speaking to your needs.
To help you figure out which option is best for your team’s needs, I’m going to walk you through the pros of both options, and some additional points you should consider about each product.
Jira Service Desk Review
SolarWinds Web Help Desk Review
Best Service Desk Software
SolarWinds Web Help Desk
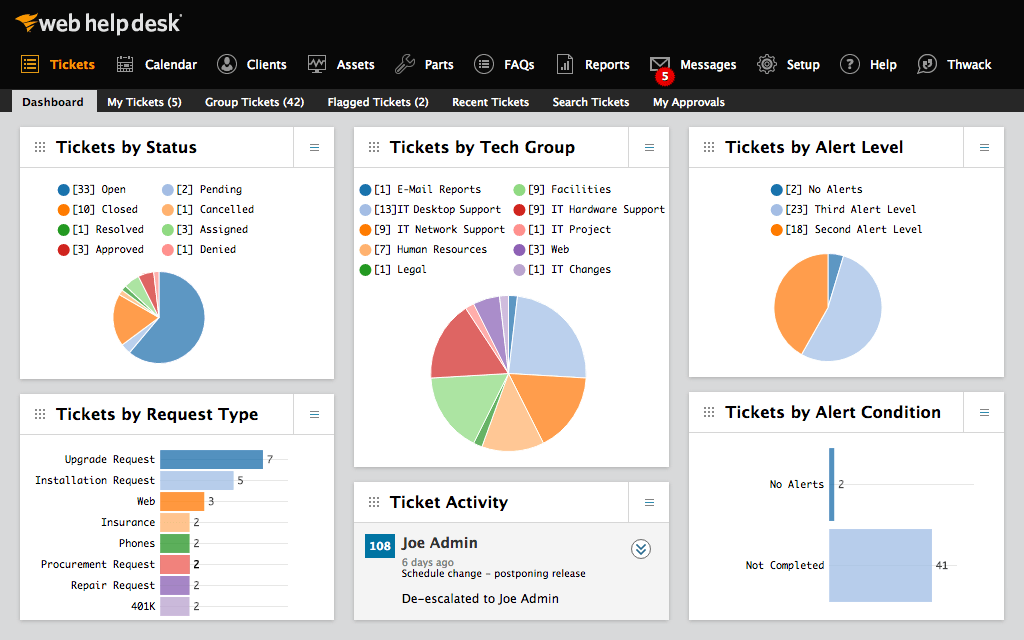
Web Help Desk from SolarWinds excels at bringing many critical ITSM capabilities under the umbrella of a single comprehensive tool. It also gets positive feedback from users for its automated functionalities, especially when it comes to streamlining ticket management, handling assets, and navigating what can otherwise be a complicated change management pipeline. Like Jira, Web Help Desk comes with a powerful knowledge base working to connect users with the relevant information and institutional IT tips and tricks.
Another reason why Web Help Desk ranks well for me is the emphasis it puts on a giving everybody what they need. It makes it easier to manage customer satisfaction with survey tracking so patrons are heard. You can link tickets to one another so IT professionals can have all the information they need to resolve an issue front and center. Or you can combine issue tickets into a single problem, so you can resolve multiple tickets at once or use rule-based routing to escalate tickets—which makes life easier for technicians. Your team will also enjoy the automated alerts, which ensure they always have the real-time tracking insight they need.
WHD also offers easy-to-use integrations with other SolarWinds products for additional functionality—if you already use SolarWinds Network Performance Monitor, Network Configuration Manager, or Server & Application Monitor, it’s easy to incorporate help desk capabilities with these programs. That being said, WHD alone is more than enough if you’re looking for a solid way to track and troubleshoot your hardware and software assets. Another unique WHD feature is it allows you to manage service level agreements and license deadlines in coordination with all your other ITSM tasks.
Jira Service Desk
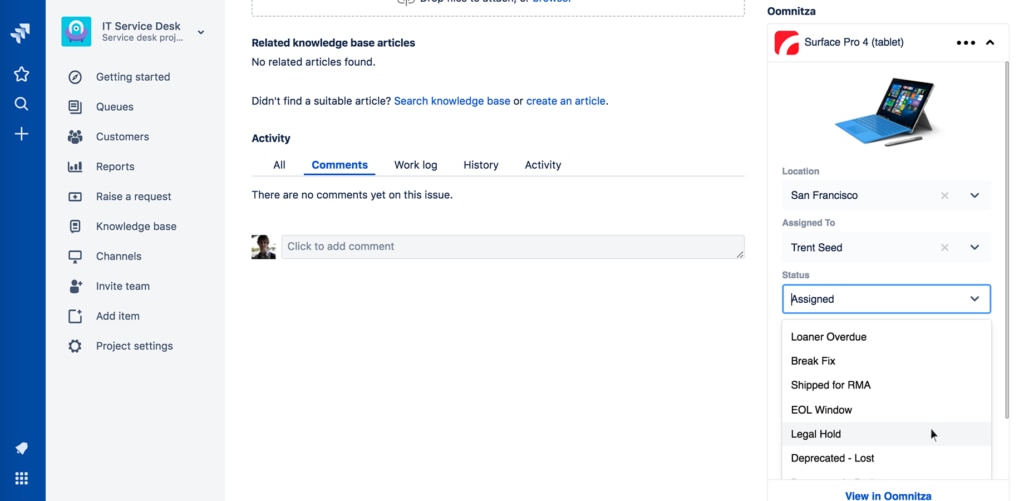
Jira Service Desk offers IT professionals a fairly comprehensive range of tools specifically designed for the ITSM lifecycle. At the earliest stages of an IT request, Jira gives end users a self-service portal and a knowledge base—if you add Confluence to your Service Desk—to connect them with tools to potentially cut down the IT workload. If end users make a formal IT request, agents can access customizable queues to prioritize, manage, and delegate pending requests based on the level of priority.
Tech professionals also give Jira high marks when it comes to incident response. The platform allows users to set up rules to automatically handle certain kinds of incidents and, with the Opsgenie add-on, makes it easier to send urgent notifications to the right people so they can act as quickly as possible. Throughout the rest of the ITSM lifecycle, Jira offers this kind of visibility and customizable control, allowing users to create a platform fitting their needs and their brand.
While Jira Service Desk tends to get solid user reviews, there are some concerns you may want to consider. For example, some users report Service Desk comes with a steep learning curve, this means realizing ROI will take some time as IT teams learn how to use it. Additionally, it’s also been noted the platform can become slow depending on how many open requests you have and it could offer more in the way of customization.
Additionally, although Jira offers a competitive array of ITSM functionalities, getting the most out of the platforms sometimes depends on investing in add-ons, such as Confluence or Opsgenie. These features are solid and I find them helpful, but businesses looking for the most cost-effective solution out there may not like having to pay for additional programs on top of the ITSM platform they’ve already purchased.
Best Service Desk Software
My personal pick is Web Help Desk from SolarWinds. I find its automated functions are incredibly reliable and genuinely saves time for IT staff to use on more pressing matters. Plus, critical features such as the centralized knowledge base are available for everyone at no extra charge, giving the platform a good bang for your buck. You can try WHD absolutely free for 14 days.