Today’s business world is seeing an increase in complexity, with more applications, devices, and categories of users to monitor every day. Naturally, this proliferation also means an increase in access points and connections, which could potentially open more doors for cyberattacks.
With security breaches constantly on the rise, every organization’s network administration strategy needs to be aware of who has access to their digital resources. In fact, 80% of data breaches involve the use of compromised credentials. Because an organization’s Active Directory contains so much information about its users and devices in the network, access management to delegate permissions is essential in preventing privilege abuse and data theft. This is why I suggest using a tool like SolarWinds® Access Rights Manager™ (ARM) to automate and streamline access management and ultimately reduce delegation errors.
The article talks about the following:
- What Is Active Directory?
- What Is Delegating Control in Active Directory?
- Using the Delegation of Control Wizard to Assign Permissions
- How to Check User Delegation in Active Directory
- How to Remove Delegation in Active Directory
- Active Directory Delegation Best Practices
- Using an Identity Access Management (IAM) Tool to Delegate Control in Active Directory
What Is Active Directory?
Developed by Microsoft for Windows, Active Directory uses structured data storage to enable IT administrators to manage user accounts and control access to network resources. Securing your Active Directory domain is of vital importance, as privileged user accounts are often the target of cyberattacks to enter an organization’s network.
At its core, securing Active Directory means using built-in login authentication and user authorization. But to further secure Active Directory once it’s been deployed, there are a few additional steps IT admins can take:
- Force domain users to use strong passwords to reduce the risk of intelligent guessing and dictionary attacks
- Enable audit policy to notify of actions potentially posing security risks
- Assign user rights to new security groups so a user’s administrative role in the domain is specifically defined
- Enforce account lockouts on user accounts to decrease the risk of an attacker compromising the domain via repeated login attempts
- Enforce password history on user accounts
- Authenticate the validity of each user through public-key cryptography
- Restrict user, group, and computer access to shared resources via filtered Group Policy settings
- Use strong encryption techniques to secure account password information on local computers, servers, or domain controllers
To minimize security breaches and privilege abuse, admins can divide and conquer via delegation in Active Directory. This delegation is a critical component of security and compliance. To delegate control, the domain admin would grant non-domain admins certain permissions in the Active Directory environment, such as the ability to create, delete, and manage user accounts in a specified organizational unit (OU).
What Is Delegating Control in Active Directory?
Creating delegated permissions ties directly into access management, a security operation designed to prevent users from accessing unauthorized levels. One of the most important methods to secure data, access management effectively manages user information, roles, and groups as well as policies needing to be enforced. Access management activities may include permission analysis, user provisioning, security monitoring across Active Directory, and running configurable reports with both current and historical visibility into access rights.
By delegating administration, IT admins can assign a range of tasks to different users and groups. For example, they can assign basic administrative tasks to regular users, while members of the Domain Admins and Enterprise Admins groups (I will elaborate on these admins later in this document) can be tasked with more domain-specific administration.
To delegate control to a particular group in the domain, admins can create organizational units. For example, the admin can assign a user the control of all accounts in a particular department, such as human resources. In a different scenario, you can assign a user administrative control only to some resources within the human resources department, such as computer accounts. You can also assign a user the administrative control for the human resources organizational unit but not any organizational units contained within it. How you decide what organizational units to create versus which should contain accounts or shared resources depends on your organization’s structure.
When domain admins understand how to delegate administrator privileges in Active Directory, they can limit access where possible, minimizing the risk of data leaks. In the case of a security breach, they can also quickly trace activity back to the source. Administrative control can be assigned to a user or group by using the Delegation of Control Wizard, which we’ll expand on below.
Using the Delegation of Control Wizard to Assign Permissions
The Delegation of Control Wizard, as its name suggests, allows admins to easily delegate administrative tasks and permissions to a user or a group using a wizard. The following steps will guide you through the process of assigning those tasks. As a best practice note, ensure users who will be assigned administrative control of objects have received adequate training.
- Open “Active Directory Users and Computers” or “Active Directory Sites and Services,” depending on the object you wish to delegate.
- On the left, browse to the object over which you want to delegate control.
- Right-click on the object. Select “Delegate Control.” Click “Next.”
- Click the “Add” button and use the Object Picker to select the users or groups to which you want to delegate control. Click “Next.”
- If the task you want to delegate appears under “Delegate the following common tasks,” check it and click “Next.” However, if the task doesn’t appear, select “Create a custom task” to delegate and click “Next.” If you selected the latter, you’ll proceed to two additional steps:
- Select the object type you wish to delegate. Click “Next.”
- Select the permissions you wish to delegate. Click “Next.”
- Congratulations; you’ve successfully delegated control over an object in Active Directory to a user or group.
How to Check User Delegation in Active Directory
Data is constantly moving, and responsibilities are always shifting. As such, permission levels need to be constantly reviewed. Here’s how to check user delegation permissions:
- From “Users and Computers,” select the “View” menu and make sure “Advanced Features” is checked. This will allow you to see the security tab when you choose “Properties” in the next step.
- Right-click on the OU for which you wish to check user delegation. Choose “Properties,” then the “Security” tab. From there, select the “Advanced” tab.
- You should now be able to view a list of all the delegated permissions on this OU.
How to Remove Delegation in Active Directory
Just as admins need to often add and view delegation, Active Directory commonly sees the need to remove those delegated permissions. Here’s how you would go about it:
- From “Users and Computers,” select the “View” menu and make sure “Advanced Features” is checked. This will allow you to see the security tab when you choose “Properties” in the next step.
- Right-click on the OU with the delegated permissions you wish to remove. Choose “Properties,” then the “Security” tab.
- Choose “Advanced.” Scroll until you find the group with the permissions. There should be a “Reset Password” permission listed under “Access.”
- To remove this permission, select it and click “Remove.”
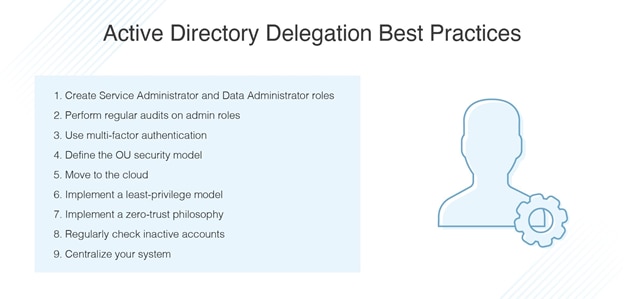
Active Directory Delegation Best Practices
To ensure the stability and long-term effectiveness of Active Directory security, keep these general best practices in mind to maximize the power of delegation.
- Create the following recommended administrator roles and assign them proper responsibilities:
- Service Administrators:
- Enterprise Admins: Responsible for top-level service administration across the enterprise.
- Domain Admins: Responsible for top-level administration across the domain. These should be a handful of trusted administrators.
- Tier 4 Admins: Responsible for service administration across the domain and are granted only the permissions necessary for their day-to-day responsibilities.
- Data Administrators:
- Tier 1 Admins: Responsible for general management of directory objects, such as password resets and modifying user accounts.
- Tier 2 Admins: Responsible for the selective creation and deletion of user and computer accounts.
- Tier 3 Admins: Responsible for management of all data administrators.
- Regional Admins: Responsible for the management of their local OU structure, with permission to create most objects within their OU.
- Perform regular audits on the administrator roles. This will help identify who may be abusing their privileges.
- Use multi-factor authentication for an extra layer of security. Weak passwords are often the leading reason for data attacks. Examples of multi-factor authentication include pairing passwords with a verification code on mobile devices, push notifications, facial recognition, or a fingerprint.
- Define the OU security model. OUs should be implemented properly with the correct objects (users, groups, computers) assigned to them.
- Move from on-premises to the cloud. Rather than spending manpower and money to keep hackers at bay from attacking on-premises data centers, organizations have seen a wealth of security from using cloud service providers. Contrary to popular belief, moving to the cloud means extra security in the form of patch management, encryption, integrations, and secure access requirements.
- Implement a least-privilege delegation model to properly ensure a secure IT environment. Remember, this can be achieved through the “Delegation of Control Wizard.”
- Like the least-privilege delegation model, implementing a zero-trust philosophy—the belief users and applications should not only undergo identity verification but continue to follow security measures until after leaving the network—is useful, especially in a time when more people are working remotely outside of their corporate networks.
- Perform regular checks of inactive accounts. Organizations will inevitably see constant change. Juggling numerous accounts in such an environment easily leads to improper offboarding and deprovisioning. The result is orphaned accounts containing user information with no assigned user, allowing hackers to potentially gain credentials and false identities.
- Centralize your system. With so many users, applications, databases, portals, and devices floating around in an organization, it’s easy to overlook some critical elements as the enterprise grows. Investing in an identity access management solution will provide the 360-degree visibility organizations need to see who has access to what while satisfying all of the above best practices.
To read more about Active Directory best practices click here.
Using an Identity Access Management (IAM) Tool to Delegate Control in Active Directory
As you can see, between managing access for thousands of user accounts, setting departmental policies, and more, access control configuration for Active Directory is a challenging and complicated web of management for IT administrators. A robust identity access management tool like SolarWinds Access Rights Manager makes the process much simpler. A centralized platform providing admins a more streamlined process for managing access privileges, ARM integrates with Active Directory and offers automated and cloud-based solutions designed to lighten manual work and maintenance.
In short, IAMs monitor who’s accessing the system, set permission levels and user roles, and track account activity to prevent privilege abuse. ARM achieves all this and more. Designed specifically to make access management easy, this SolarWinds software sets itself apart from other IAM solutions by combining user authorization configuration with network security enhancements. As such, it extends the capabilities of Active Directory to deliver greater control over user credentials. When admins analyze access permissions, they can see who has access to what, when they accessed it, and logs of past changes. By using ARM to ensure the principle of least privilege—granting users the minimum level of access they need to perform their day-to-day responsibilities—admins can help curb the risk of security breaches. After admins define data categories, the software will automatically delegate and provision user access rights as needed.
ARM also generates customized reports to help you demonstrate compliance with regulatory requirements. Admins can create highly customizable and easy-to-understand reports for both internal stakeholders and external auditors.
SolarWinds ARM does more than just manage user account access rights. The software can identify threats from irregular account activity and detect vulnerable inactive accounts. As today’s digital-reliant world continues to see a rise in IT security risks, having an access rights management system designed to also act as a data loss prevention system and data compliance auditing tool is more important than ever. As such, SolarWinds Access Rights Manager continues to stand out as an industry-leading choice. Users can test out the comprehensive features of ARM on Windows Server with a fully functional 30-day free trial.
