When it comes to running your organization, security is probably a top priority. However, there are a lot of different digital safety measures to consider. You may have heard about the principle of least privilege (PoLP), but you may not know exactly how it can help.
Fortunately, the principle of least privilege can provide your business with several advantages. By understanding how to leverage this simple strategy, you can start improving both your security and your productivity.
In this article, we’ll introduce you to the principle of least privilege. Then, we’ll walk you through three important reasons why you should consider using it.
What Is the Principle of Least Privilege?
One of an IT admin’s many tasks is to decide which employees have access to which resources. The more efficiently they do this, the more productive your organization can be. However, it’s not always an easy job.
If they’re too generous with their permissions, they could risk a malicious actor gaining access to your system. By the same token, well-meaning employees who end up in a high-level area may accidentally make catastrophic changes.
On the other hand, too little access can also be an issue. This can lead to workers constantly needing to request permission. Fielding these requests can be draining on those who control this access.
Fortunately, the principle of least privilege can resolve both issues. The foundational elements behind it are simple: each user gets access to the required resources for a specific task only. No more, no less.
This straightforward approach eliminates the need for technicians to maintain an intricate and ever-changing permissions system. By applying this strategy, you can keep your information safe while also saving your team time.
3 Key Reasons to Use the Principle of Least Privilege
1. It Helps Keep You Safe From Cyberattacks
Implementing least privilege can help defend against security threats. A lot of your best practice rules probably center around keeping your data safe. Carefully calibrated access controls are a subtle yet important part of this strategy.
For example, let’s say a user account that only needs low-level clearance gets access to your most sensitive data. These workers may not have the same technical knowledge as those who are well-versed in these delicate areas. This could lead to several weak spots in your network, which would make it easier for bad actors to access your data.
The principle of least privilege works against this by limiting unnecessarily privileged accounts. This kind of defense can also protect against attacks like SQL injections. If fewer people have high-level access, there are fewer ways your organization can be impacted if the virus spreads.
High-quality PoLP software can help you double down on this benefit with on-demand visibility reports.
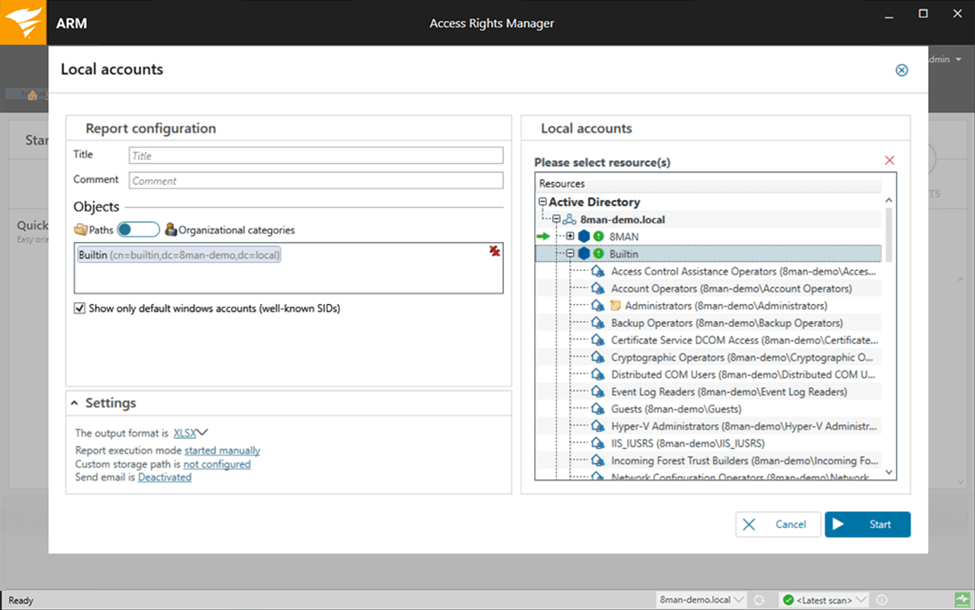
Automation is a wonderful feature, but sometimes a manual approach can be effective as well. By staying informed and in control of these permissions, you can help your organization avoid potential security pitfalls.
2. It Can Improve Productivity Across Your Organization
Rigorous security standards aren’t always simple. They can take up a lot of time and energy. As such, it’s normal to feel they’re undermining your organization’s productivity. Fortunately, the PoLP’s very nature means it can benefit your efficiency by helping you eliminate the repetitive, time-consuming task of administrating constant requests for access. Some may be necessary, while others may not be. An automated system operating under the PoLP can sort through these requests instantly.
As a bonus, this automation can reduce the odds of unnecessary permissions being granted. The result is less work all around. Since it takes some pressure off of your security staff, they can use the saved time to focus on other security measures.
To make the most of this benefit, we recommend you look for a tool that standardizes this process even further. One option is to start with the users themselves.
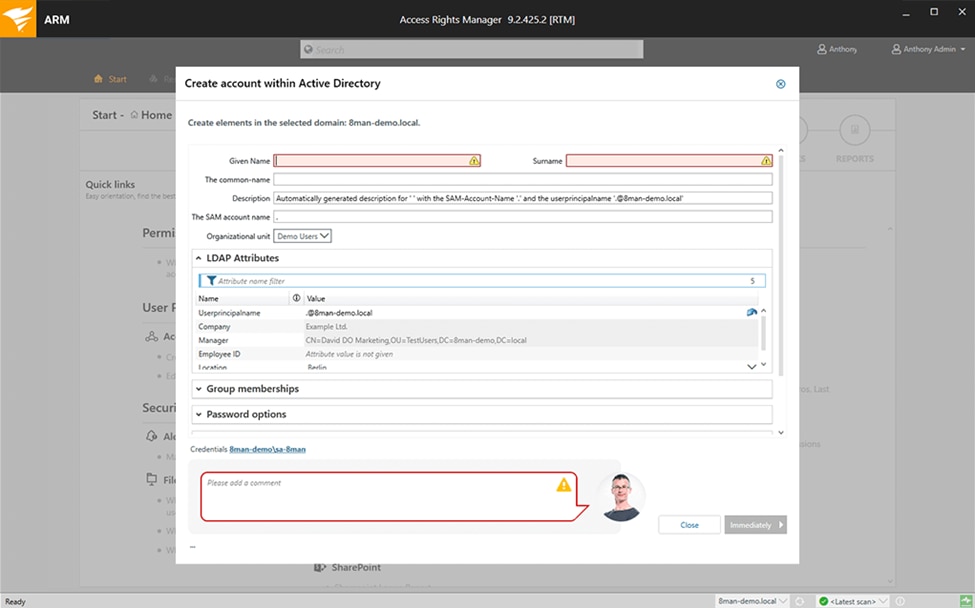
SolarWinds® Access Rights Manager (ARM) can streamline your approach with role-specific templates, so you can keep permissions limited to certain titles. However, you can still make manual changes for any exceptions.
3. It Can Help You Keep More Detailed Records
Recordkeeping can help guide your growth or understand any abnormalities. No matter how confident you are about your security standards, you probably want a detailed summary to look back on.
Records are essential for compliance reasons. With detailed and updated permission reports, you can look forward to a streamlined auditing process. This goes double for any program that can automate your data collection: there’s usually less work involved and less room for error.
Reviewing summaries of how the principle of least privilege has been applied in your organization can also be helpful for your analysis. In-depth information about who made what changes, using which permissions, can help you spot incorrect access rules before they become problems.
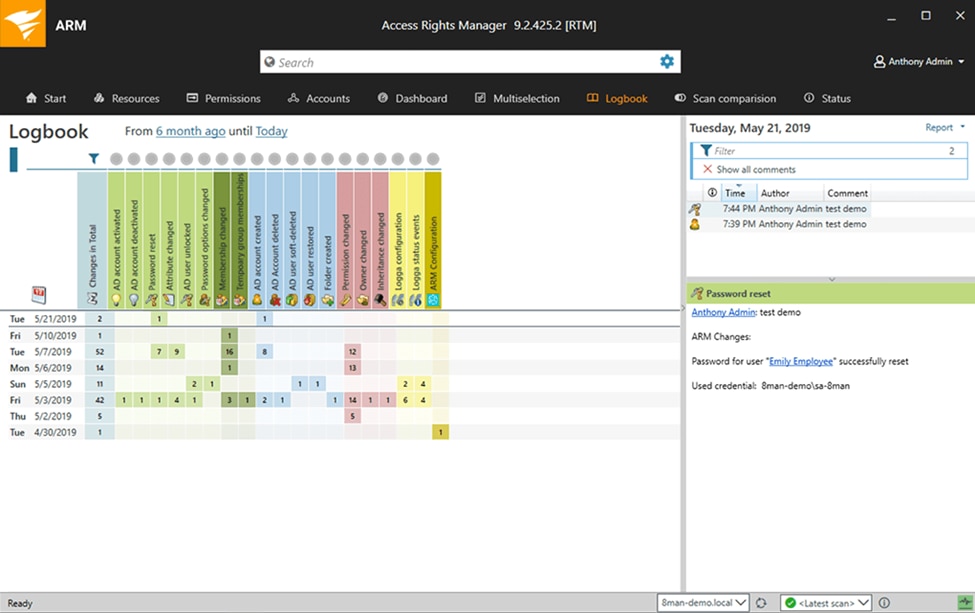
You can opt for an organization-wide summary or an analysis of a single user’s actions. With this kind of information, you can ensure the PoLP is being correctly applied in all areas of your business.
Conclusion
If you’re worried about access rules putting your information security at risk, you’re not alone. Fortunately, you can take steps to defend your organization. By implementing the least privilege rules liberally, you can limit the possibility of a dangerous data breach.
In this article, we covered three ways the principle of least privilege can benefit your business:
- Limiting the number of privileged accounts helps reduce the risk of cyberattacks.
- Streamlined rules can boost productivity.
- More insightful information can improve your organization’s recordkeeping.
Do you have any questions about the principle of least privilege? Let us know in the comments section below.

