With the three pillars of observability considered more or less canon for IT monitoring philosophy these days, and logging being one of those pillars, it’s important to understand the tools, systems, and solutions that help IT practitioners do a good job of aggregating, normalizing, and leveraging logs in all their forms to provide improved insight into application and system health.
- Kiwi Syslog Server
- SolarWinds Security Event Manager
- ManageEngine EventLog Analyzer
- Datadog
- Fluentd
- Graylog
- SolarWinds Log Analyzer
- Sumo Logic
- ELK Stack
- Papertrail
- Loggly
- WhatsUp Management Suite
- Mezmo (Formerly LogDNA)
- Syslog-ng
- GoAccess
Best Log Management Software List
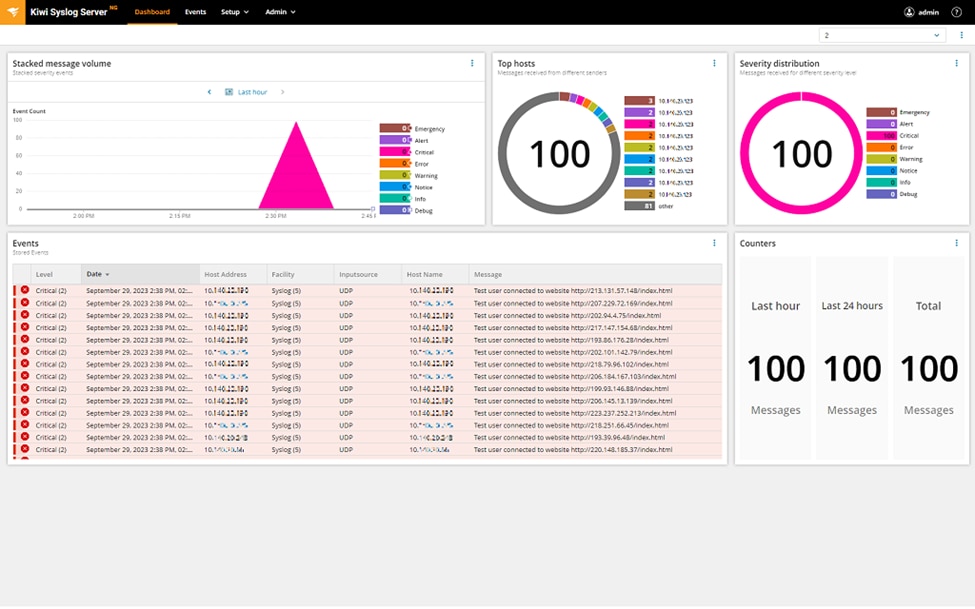
1. Kiwi Syslog Server
© 2024 SolarWinds Worldwide, LLC. All rights reserved.
Kiwi Syslog Server acts as a syslog and trap receiver, using rules to filter those messages based on source, keywords, and other patterns before processing them in a variety of ways. You can receive messages from an unlimited number of sources and have a dozen processing options at your disposal, including transparent forwarding, storing in a database, running an external program or API, and more. You can manage syslog messages from different network devices like Linux, UNIX, and Windows.
With this centralized log management tool, there’s no need to comb through endless logs on a system basis. Instead, you’ll be able to manage your SNMP traps and syslog messages with a single console, saving time and energy. To save yourself even more effort, you can configure Kiwi Syslog Server to automatically run scripts, log to file or ODBC database, forward messages, or send email alerts in almost real-time if it detects a problem with your server or devices.
If you’re after log management tools that provide a filtration layer capable of scaling out and handling a large number of messages, look no further than Kiwi Syslog Server. One installation will be more than enough for many environments. But if not, you can always add another. Moreover, in October 2023, SolarWinds released a new generation of Kiwi Syslog Server, bringing new UI, including an interactive dashboard and significant performance and security improvements.
Kiwi Syslog Serveris a native web-based application, meaning you can work on the go, and automated log archival and cleanup, enabling you to better comply with HIPAA, PCI DSS, and SOX regulations. Ultimately, Kiwi Syslog Server is an incredible option if you need to manage syslog messages, SNMP traps, and Windows event logs.
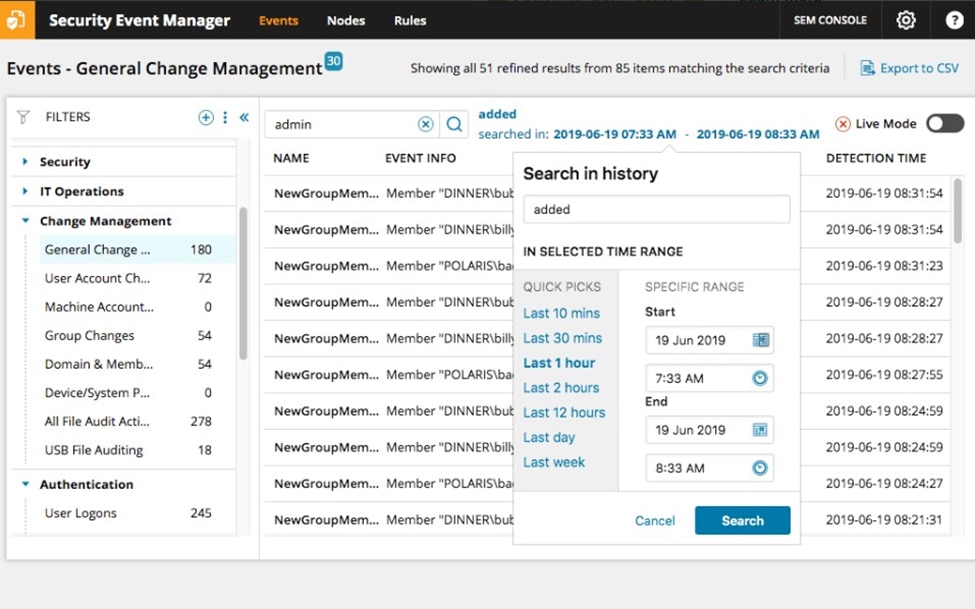
2. SolarWinds Security Event Manager
© 2024 SolarWinds Worldwide, LLC. All rights reserved.
SolarWinds Security Event Manager (SEM) straddles the line between a “simple” log file aggregation and management platform with threat intelligence and a full Security Information and Event Management (SIEM) solution. It combines the ability to receive messages from a variety of sources and normalize and aggregate them together with a powerful analytics engine that helps identify potentially system-impacting events. In addition, you can use Security Event Manager to validate compliance, thanks to reporting purpose-built for HIPAA, PCI DSS, SOX, DISA STIG, and more.
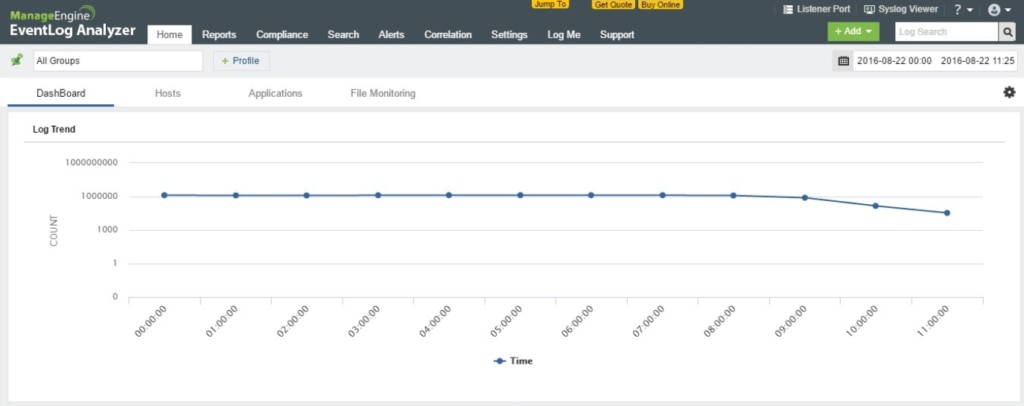
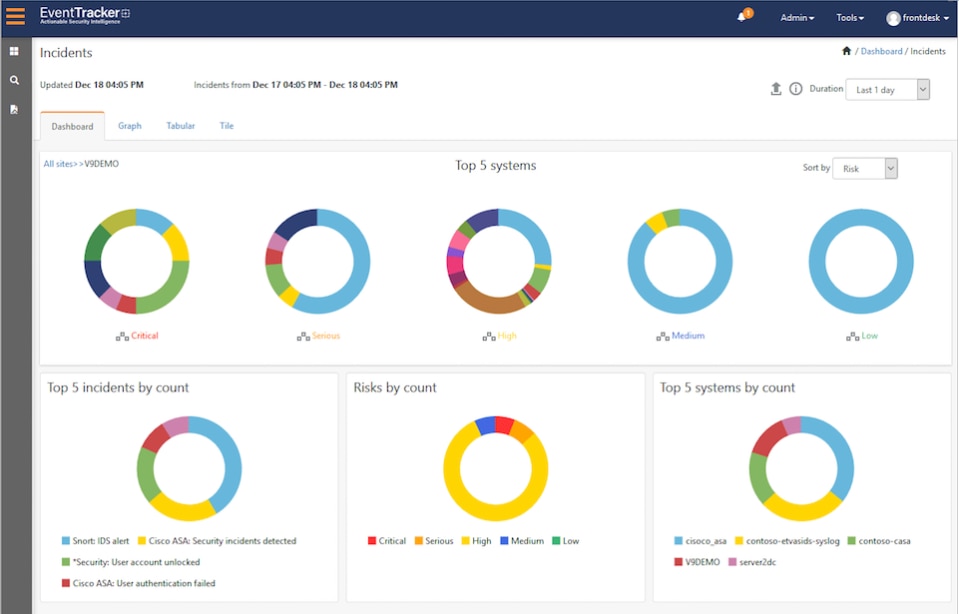
3. ManageEngine EventLog Analyzer
© 2024 Zoho Corporation Pvt. Ltd. All rights reserved.
ManageEngine is another trusted name for monitoring professionals. With the ability to collect, manage, analyze, correlate, and search through the 700 sources of log data and handle up to 25,000 messages per second, it’s worth a look. With the ability to do forensic analysis of past events as well as leverage real-time pattern matching, it has the potential to minimize security breaches. It comes preconfigured with over 30 rules to identify brute force attacks, account lockouts, data theft, web server attacks, and more. Finally, the log parser is highly customizable.
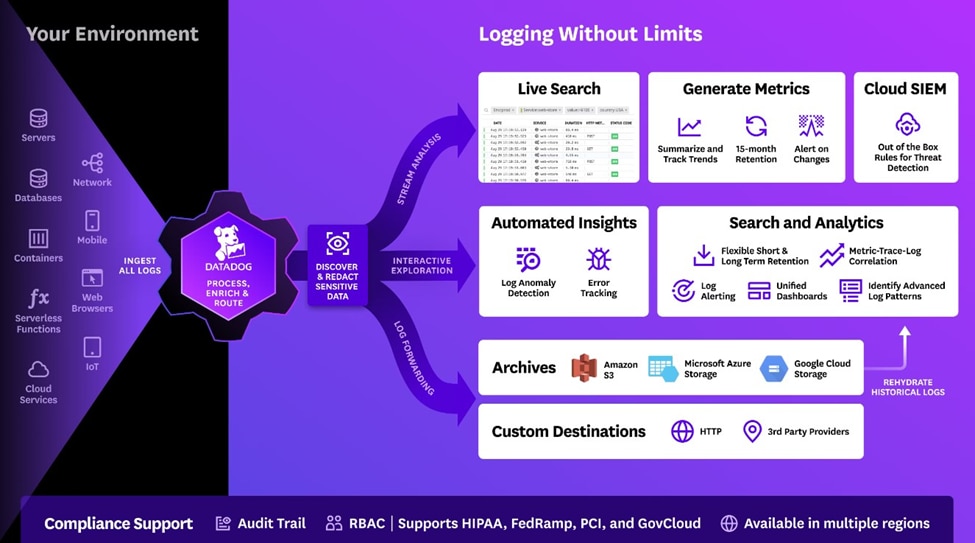
4. Datadog
© Datadog 2024
Datadog Log Management is a user-friendly solution that can provide deep insights and valuable context for analyzing log data. With this log management tool on your side, you’ll gain complete visibility across your stack in a single view. Whether you want to see logs, metrics, or traces, Datadog Log Management has you covered. Plus, you can get to work quickly, thanks to Datadog Log Management’s many out-of-the-box log processing pipelines. They offer pipelines for over 200 common technologies.
You can easily search for, filter, and analyze logs, all without using any querying language. Instead, you can use interactive dashboards combined with drag-and-drop data visualizations to analyze your logs. You can also rely on Log Patterns to provide valuable insights into log activity trends or use the Pattern Inspector to view distribution values within each log pattern. If you want log management tools that can automatically identify anomalies in your logs, Datadog Log Management can do that, too. Just use Watchdog Insights.
Other notable Datadog features include the ability to:
- Route processed logs to 3rd-party destinations using Log Forwarding
- Generate metrics from all logs, indexed or unindexed, to track KPIs and trends
- Rehydrate logs from compressed archives
- Pivot from logs to triggered security signals without changing tools or contexts, allowing for faster troubleshooting
- Use granular RBAC controls to manage log data access
- Send and process millions of logs each minute
5. Fluentd

©2010-2024 Fluentd Project. ALL Rights Reserved.
When it comes to log management tools, Fluentd is one of the best open source options. As a data collector, Fluentd can help you unify the data collection and consumption process. It provides a unified logging layer between backend systems and data sources, ultimately decoupling the two.
At its core, Fluentd is quite simple. In fact, you can set it up in less than ten minutes. However, it has more than 500 plugins available, meaning you can easily connect this solution to all your data sources and outputs. If one of the existing plugins doesn’t suit your needs, you can also easily write and deploy your own plugin to fill the gap.
Fluentd also has built-in reliability in the form of its memory- and file-based buffering and support for robust failover. It has a small memory footprint of 30-40 MB and has a robust community-driven QA/Support. So, it’s hardly surprising that over 5,000 companies already rely on Fluentd, including big names like Atlassian, Nintendo, and Twilio, with the largest user collecting logs from more than 50,000 servers.
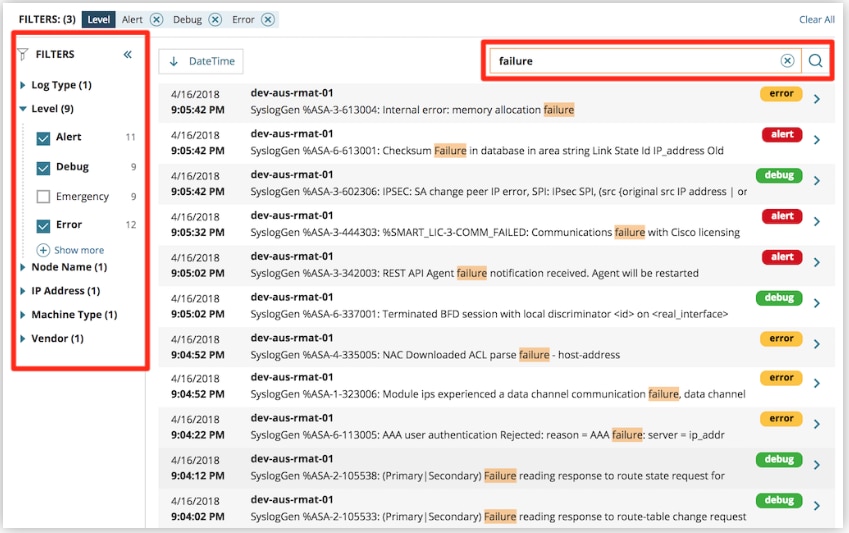
6. Graylog
© 2024 Graylog, Inc. All rights reserved
Graylog also ranks among my top log management tools. This industry-leading solution was designed to help organizations combine, query, and visualize their log data in a centralized location.
With Graylog, spotting trends and pinpointing anomalies is simple, thanks to the tool’s powerful visualization capabilities. You can easily customize Graylog’s dashboard using data widgets to ensure that you see what matters most first. If something piques your curiosity or sets off your alarm bells and you’d like to have a more in-depth look at something, Graylog will allow you to drill down to discover more detailed information.
You can also take advantage of Graylog’s advanced search functions to gain a deeper understanding of your data. In fact, Graylog can search terabytes of data to return answers to your queries in mere milliseconds, meaning you can quickly identify and resolve any issues. To save even more time, you can save searches. You can even share them to ensure everyone on your team is on the same page.
Graylog also features robust alerting and reporting capabilities. You can receive alerts via email, Slack, PagerDuty, SMS, and more. Graylog will also allow you to set alert thresholds, ensuring you only receive an alert when it really matters. On the reporting side of things, Graylog has worked hard to simplify the process. You can configure Graylog to send regular reports directly to your email inbox within minutes.
7. SolarWinds Log Analyzer
A relative newcomer on the scene, Log Analyzer was released in mid-2018 and acts either as an add-on to the existing suite of SolarWinds monitoring tools or as a standalone logging solution.
© 2024 SolarWinds Worldwide, LLC. All rights reserved.
Focusing on syslog and trap, the strength of this tool lies in its visualization capabilities and powerful searching engine, which can filter and search past events or perform those same actions on the logs as they are received in real time.
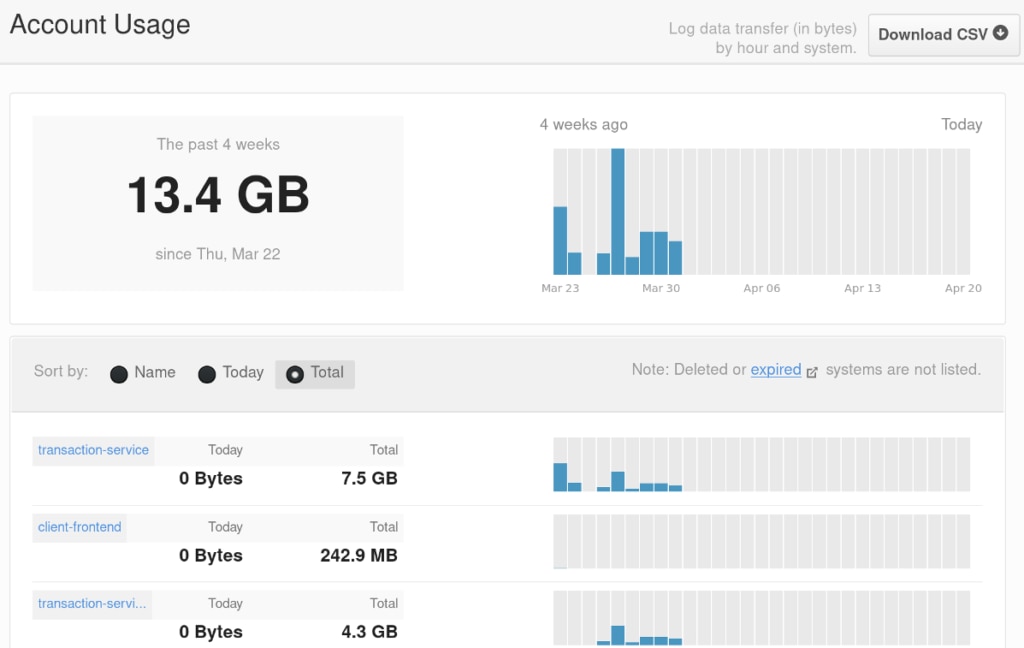
8. Sumo Logic
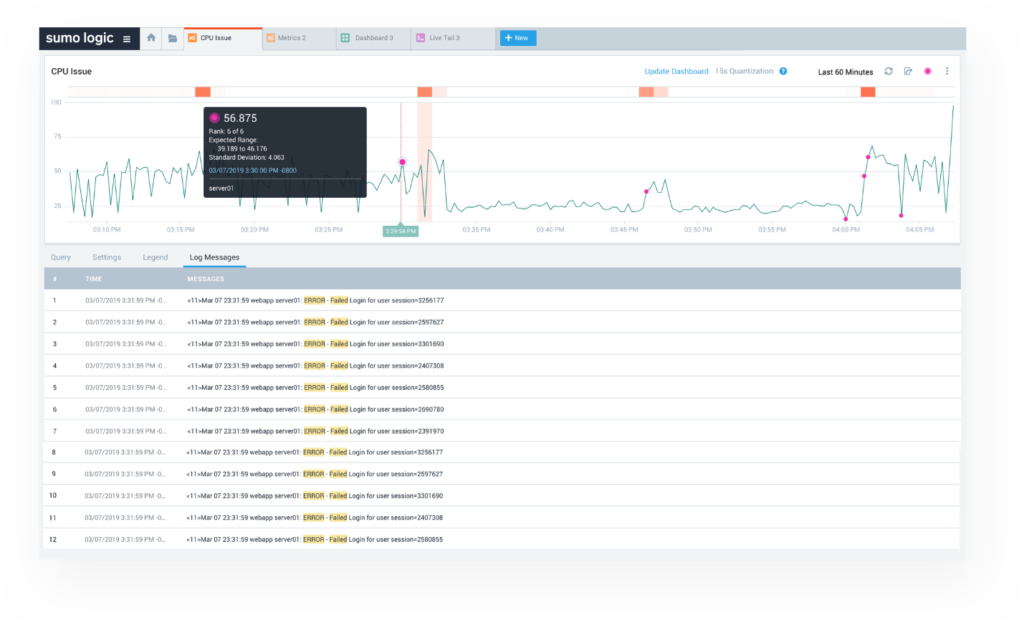
©2024 Sumo Logic
Originally created to be a SaaS version of Splunk, it has since evolved into an enterprise-class log management tool in its own right. With the ability to analyze log data in real-time and apply machine-learning, Sumo excels at finding root causes for specific errors or events and therefore makes it a perfect fit for the security and compliance use-case. Just remember that it’s agent-based, so that is going to add some overhead to the ongoing management and deployment.
9. ELK Stack

© 2024. Elasticsearch B.V. All Rights Reserved
“ELK” is the combination of three open-source tools: Elasticsearch, Logstash, and Kibana. Logstash processes the data on the server side and then funnels it to Elasticsearch, which provides the search and analytics capabilities. Finally, Kibana allows users to visualize that data in charts and graphs. If it sounds like the IT version of building a prefab furniture piece, you wouldn’t be far off. That said, many people enjoy the feeling of total control and ownership. And the cost (free, if you don’t count the doesn’t actual cloud hosting charges) is an added bonus.
10. Papertrail
© 2024 SolarWinds Worldwide, LLC. All rights reserved.
SolarWinds® Papertrail™ cloud-hosted log management can be installed typically in under a minute and connected to the servers you want to monitor even faster than that. The most compelling aspect of this tool is the ability to do lightning-fast searches of log events in real time, as well as the live tail feature.
But the clean, intuitive interface doesn’t hurt either. Papertrail lets you interact with your data via the browser, command line, or an API. That said, Papertrail is for the IT pro who’s not interested in flashy extras and wants a straightforward log file analyzer and aggregator.
11. Loggly
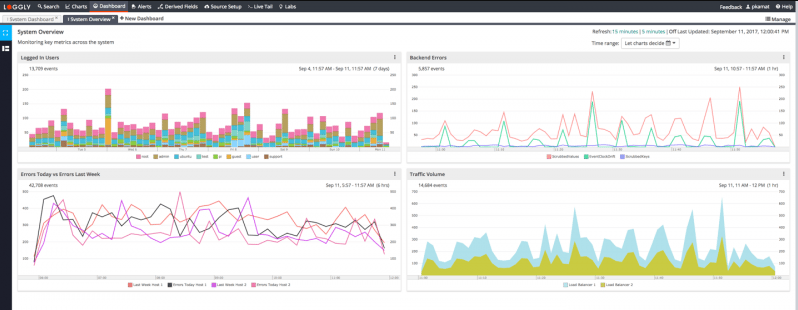
© 2024 SolarWinds Worldwide, LLC. All rights reserved.
SolarWinds Loggly® log management and analysis tool was created by—and for—DevOps practitioners. It has robust analytic capabilities, but the UI was built to be as easy to navigate and use as possible. It was also built to efficiently cull through enormous volumes of log data, and surface trends that might be overlooked over time by other tools.
These features make it a perfect tool for the kinds of troubleshooting performed as part of customer support, rather than pure development with mocked-up data. As you would expect from such a tool, there’s a full REST-ful API that comes along with it, meaning it can be integrated into other tools in a multitude of ways.
12. WhatsUp Log Management Suite
Copyright © 2024 Progress Software Corporation and/or its subsidiaries or affiliates. All Rights Reserved.
For many IT practitioners, IPSwitch’s WhatsUp Gold is their first experience with a log monitoring tool. WhatsUp Log Management Suite is an automated tool that collects, stores, archives, and saves system logs, Windows events, and W3C/IIC logs. On top of that, it performs ongoing pattern analysis, so it can trigger alerts based on abnormal activity. The types of events tracked include access rights and file, folder, and object privileges. It can also use collected data for compliance reports for HIPAA, SOX, FISMA, PCI, MiFID, or Basel II. In actuality, WhatsUp Log Management Suite is really a set of four integrated applications:
- Event Archiver
- Event Alarm
- Event Analyst
- Event Rover
13. Mezmo (formerly LogDNA)
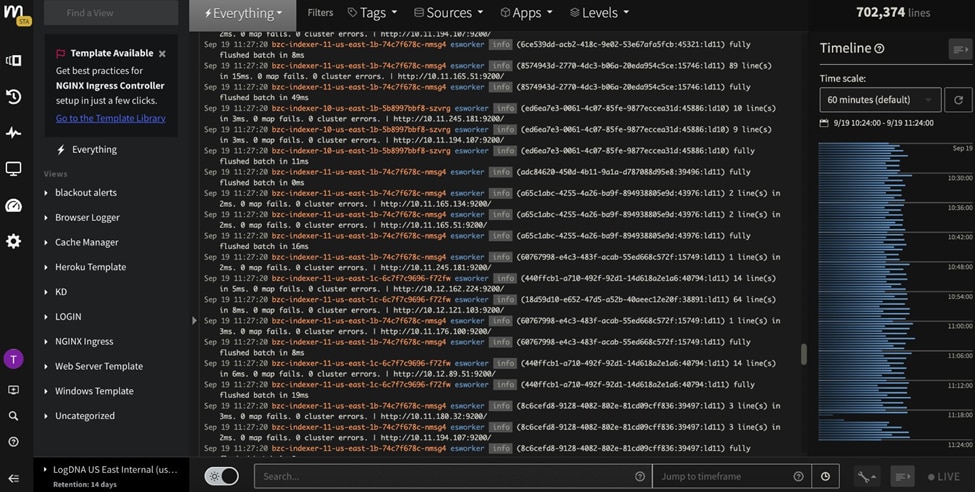
@2023 Copyright Mezmo Inc.
Mezmo (previous LogDNA) is available in either a cloud-based or a self-hosted version, depending on your preference. It scales to “hundreds of thousands of logs per second,” generating terabytes of data per day, all the while offering complete security of that data as well as real-time log analysis. Both the company and the LogDNA product itself are SOC2, PCI, and HIPAA compliant as well as Privacy Shield certified.
14. Syslog-ng
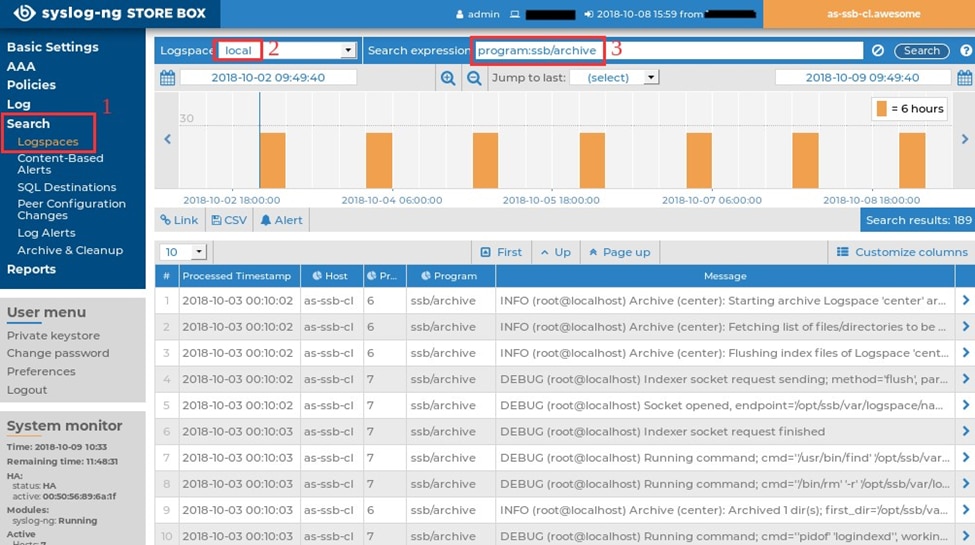
© ALL RIGHTS RESERVED.
Another of my favorite log management tools is Syslog-ng by One Identity. Not only can Syslog-ng help optimize your SIEM solution’s performance by reducing the amount of data it is fed while simultaneously improving the quality of the data it receives, but it can also help you quickly find critical logs. You can use full text queries with Boolean operators to search through billions of logs in seconds to find the information you need.
With Syslog-ng, you can collect logs from a variety of sources. This includes web servers, legacy systems, SQL databases, and devices and applications that generate jSON messages or text-based files. You can also deliver data to the Hadoop Distributed File System, the MapR Distributed File System, Elasticsearch, MongoDB, Apache Kafka, and more.
Syslog-ng is a powerful tool for universal log collection, routing, and management. Additionally, it’s quite secure with its tamper-proof encrypted storage, automated archiving, and granular access controls.
15. GoAccess
MIT Licensed
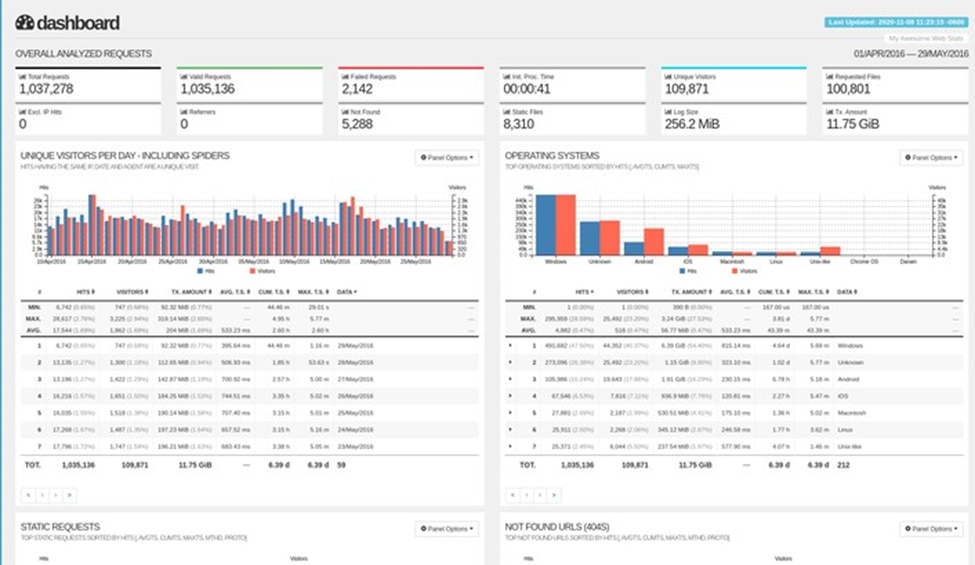
Also among my top log management tools is GoAccess, an open source, terminal-based web log analyzer written in C. With GoAccess, there’s no need to use your browser, but you’ll still be able to view and analyze web server statistics in real time. It’s easy to configure and operates in completely real time. Every 200 milliseconds, panels and metrics on the terminal output will be updated. HTML output is updated every second.
GoAccess supports nearly all web log formats, which means you can view and manage logs from Nginx, Amazon S3, Apache, CloudFront, Elastic Load Balancing, Caddy, and more. It is Valgrind tested and provides well-designed terminal and bootstrap dashboards, which you can easily tailor to match your color tastes.
With GoAccess, you can track application response time, process logs incrementally for data persistence, and expand report panels to check for correlations between various reports. As a result, you can more easily identify any aggressive hosts/crawlers/bots that are consuming your bandwidth, see which virtual host is consuming the majority of your web server resources, and determine the amount of bandwidth, visitors, hits, and metrics for the slowest running requests by hour or by day.
The Difference Between On-Premises and Cloud-Based Log Management
It’s important to clarify what’s meant by “log monitoring” for two reasons: first, because logs are present in several different forms on a variety of different systems around the enterprise. And second, those logs can be a rich source of insight for everything from security events to through application health and up to customer experience. More than that, however, is the fundamental difference in how and why on-premises logging is performed versus their cloud-based counterparts.
On-premises systems work on the presumption that:
- We clearly understand the systems involved in our application infrastructure.
- We clearly understand the substance and nature of the log messages being sent.
- Logging is “expensive” both in terms of hardware (disk storage) and performance (every log message takes processing time away from application processing).
- Logs are an information source of last (or nearly last) resort. They tell us forensically (after the crash) what happened.
- The systems that logging informs us about are fundamentally permanent. They don’t disappear often (or ever).
However, cloud-based log systems work on an entirely different set of presumptions:
- We don’t always (and sometimes cannot) know all the services and systems involved in our application infrastructure.
- In fact, we may not have access to all the systems or sub-systems. Therefore, the only window into the systems will be via the performance of the code.
- Disk, processing, and log performance are cheap to the point of having effectively zero cost. The processing impact of logging is completely decoupled from application processing.
- The systems in the cloud can be (and usually are) extremely ephemeral. By the time a human looks at a log, that system is likely gone.
The entire point of cloud-based logging is to be ever-present, infinitely scalable (both in terms of data storage and data flow), and have sophisticated analytics capabilities baked into the log management tool so that the messages, telemetry, and insight can be surfaced quickly and reliably with minimal human intervention.
The Mostly Un-Necessary Summary
Log monitoring is a vast and varied sub-specialty within the monitoring discipline, and there are solutions out there to fit almost any use case. If you are just beginning your search for log management tools for the job, I hope this has given you a head start. If you already have a log management tool and are either considering a change or addition, I recommend trying a log tool like Kiwi Syslog Server.
This affordable on-premises software is capable of helping you manage syslog messages, SNMP traps, and Windows event logs. It’s a centralized solution that will allow you to inspect log messages from your devices and will even provide almost real-time alerts when problems arise on your network devices or server. As a result, your IT department can more easily monitor logs and manage security and compliance.
