Organizations maintain hundreds of workstations, servers, and mobile devices; they all need protection from ever-growing malware applications and attacks, including worm viruses, trojans, spyware, and ransomware. Successful security breaches can cost organizations in lost productivity, damaged reputations, penalties due to failed regulatory compliance, and customer attrition.
According to a WSJ Pro Research survey, businesses with less than 10 million USD in revenue are less prepared to deal with cyberattacks than their larger counterparts. This is particularly concerning, as SMBs don’t have enough resources to recover from cyberattacks compared to larger organizations. To make sure you can help customers prevent threats, try using a managed antivirus solution that allows you to centrally manage customers’ AV statuses and gain visibility into endpoint security.
Managed antivirus solutions allow admins to deploy agents, schedule scans and updates, enforce security policies, and restrict users from disabling protection. This approach can protect endpoints against threats, isolate infected machines, and remediate security issues based on comprehensive reports.
Choosing a solutions depends on several factors, including:
- Can the solution identify and quarantine known and unknown threats effectively?
- Is the solution scalable enough to support a growing organization?
- What is the impact on system resource consumption?
- Does the solution offer flexible licensing?
- Can it support multiple platforms and virtual environments?
This article discusses some of the best managed antivirus solutions based on their features and approach to blocking malware attacks.
N-able RMM Managed Antivirus
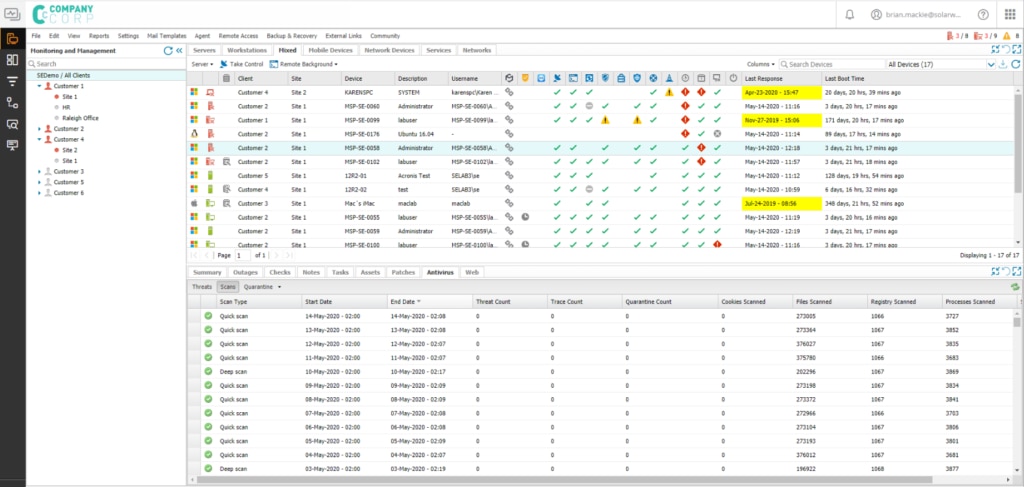
N-able® RMM is a remote monitoring and management solution designed for MSPs. It offers a wide range of capabilities, along with managed antivirus. MSPs can quickly deploy it across sites, workstations, and servers using default policies, get granular by applying organization-specific security policies for those with differing security needs, and customize rules for quarantine and virus definition downloads.
It detects and blocks known threats using signature-based scanning and performs heuristic checks in a sandbox environment to identify unknown malware—providing sophisticated protection against both known and unknown threats. It also performs behavioral monitoring and scanning in live environments to block advanced and sophisticated malware that performs malicious activity.
The antivirus feature in N-able RMM performs lightweight scans to minimize resource drain and allows MSPs to schedule deep scans around downtime to mitigate disruption to employees’ work. It sends near real-time alerts and detailed reports to help contain malware exploits early on and expedite remediation.
In addition, N-able MSP offers other security capabilities, like:
- Disk encryption manager to help you manage and monitor encryption
- Endpoint Detection and Response (EDR) for protection against ransomware and zero-day exploits—which can take you a step beyond scanning for viruses to catch other malicious threats beyond viruses and malware
- Passportal™ for enterprise-grade password protection and management
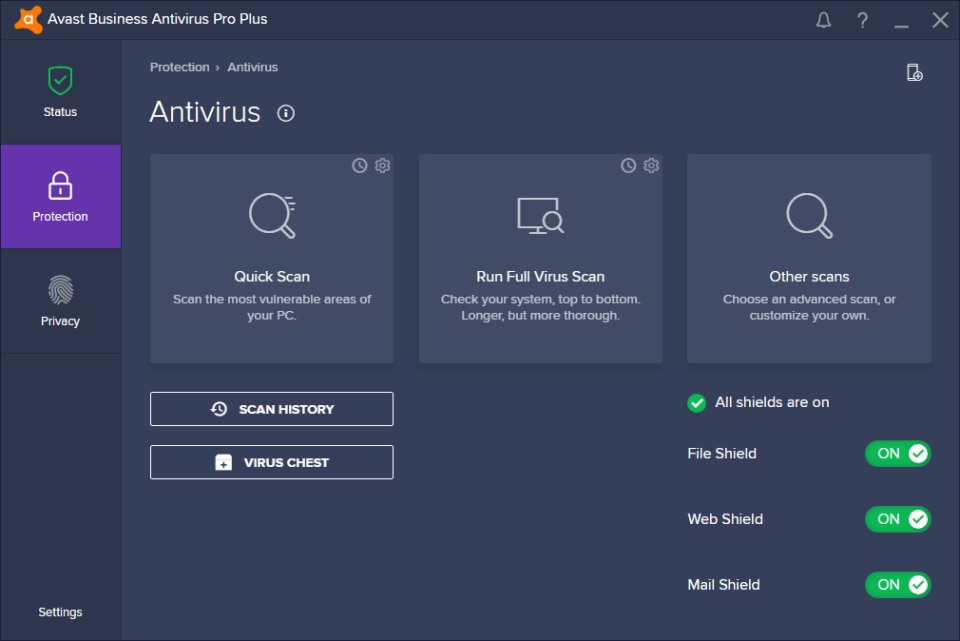
Avast Business Antivirus Pro Plus
This offering provides enterprise-grade threat protection and offers a cloud management console to centralize antivirus management. It uses a lightweight agent that responds to malware without impacting system performance and blocks malware using an algorithmic approach.
Moreover, it identifies unknown threats by employing artificial intelligence and cloud-based threat analysis. It works across various types of endpoints, including Windows, Windows Servers, Mac, and Linux.
Microsoft Defender Antivirus
Microsoft Defender is an antivirus software program built into Microsoft Windows designed to protect against viruses, malware, and ransomware (and help with overall security). It provides advanced security features with automatic scans, full-system scans, boot scans, as well as custom and scheduled scanning options to safeguard data and devices in real time. Users can also manage privacy settings based on location and data usage options.
Additionally, Windows Defender offers a second layer of data protection in its controlled folder feature. The role of this feature is to block unauthorized applications from accessing key documents automatically.
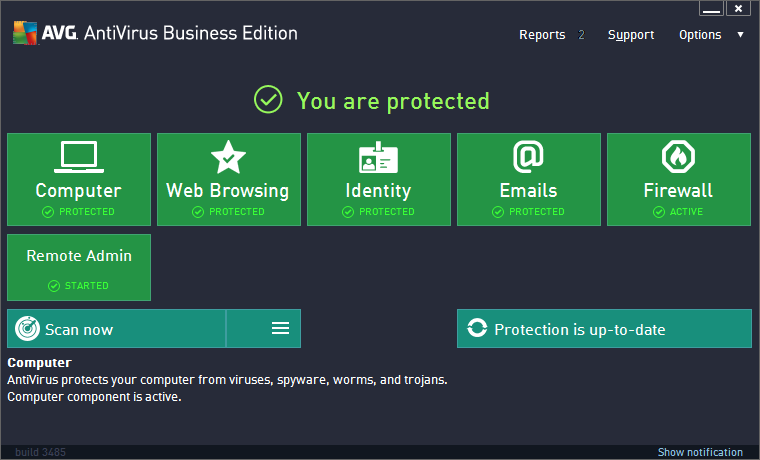
AVG Antivirus Business Edition
AVG Antivirus Business Edition protects business-critical data and sensitive information from viruses, attacks, malware, and other online threats. Businesses can quickly deploy antivirus to multiple endpoints, schedule updates, manage policies, and monitor threats.
The solution also offers identity protection, file shredders, file server security, and remote access rights to strengthen business data security. It also provides ransomware protection, a smart scanner, safe surfing, automatic updates, free phone support, and compatibility with Windows 10.
Webroot Business Endpoint Protection
Webroot Business Endpoint Protection is a SaaS-based endpoint protection solution that works across Mac, Windows workstations and servers, terminal servers, and virtualization environments. Unlike traditional approaches that require updating signatures or virus definitions, it performs malware discovery in the cloud in real time, so the agent consumes very low system resources and works even when a particular endpoint is offline using proprietary technologies. Admins can also allow or deny specific applications, automate agent updates and alerts, and schedule reporting.
Conclusion
Threat actors are increasingly using sophisticated methods and malware applications that are difficult to detect and contain. Therefore, it is imperative to enforce strong security policies and approach endpoint security proactively—with a strong managed antivirus solution.
Get More on Centrally Managed Antivirus Software
If you’d like to further explore this topic, be sure to also read:
