Email threats are becoming an increasingly large problem, both for companies and individuals. As our email addresses and personal information become more widely spread, it becomes easier to find this information online, which allows malicious actors to discover routes of attack more easily. For businesses, attacks such as phishing email threats, malware threats, and darknet email threats can leave vulnerable data and systems exposed and can cause major reputational and monetary losses.
One of the best ways to fight threats is to use an appropriate tool. Most people think of antivirus software and scanning tools in this context, but broader tools can protect your business in a much more comprehensive way, while providing other useful features. SolarWinds® Identity Monitor and SolarWinds Server & Application Monitor (SAM) are at the top of my list for preventing email threats from stealing your business information and gaining critical access.
Table of contents:
- Email Threats Definition
- Types of Email Attacks
a. Phishing Email Threats
b. Malware Threat Email
c. Darknet Email Threat - Options for Defense
a. Organizational Policies
b. Tools and Software - Best Ways to Fight Threats
Email Threats Definition
A definition of email threats is hard to form, because there are so many different kinds of threats, and the routes attackers use change constantly. Some of the most common email threats come through deception, impersonation of trusted entities, and the exploitation of private information to encourage people to click on links or download attachments. Once these attachments are downloaded, malware can be installed; if a link is clicked on, the user may be forwarded to a fake login page, at which point their credentials are stolen.
Types of Email Attacks
Many types of email attacks are occurring, but a few stand out more than others in terms of their danger to the user and the likelihood of occurrence.
Phishing Email Threats
Phishing emails involve an attacker pretending to be someone else—such as a bank or a service you’ve subscribed to—with the aim of tricking you into opening their email. The fundamental marker of a phishing email threat is the sender appears to be a trusted entity, but the email contains a malicious link.
The link can lead either to a download of malware or to a fake webpage, such as a bank login page. If you then log in to your bank through the link, the malicious attacker gets your login credentials. In many cases, phishing attacks are used to gain entry to corporate networks—for example, by compromising employee accounts and allowing the attacker to bypass security measures.
Malware Threat Email
Like phishing email threats, malware can be sent through an email. You’ll know it’s malware if, for example, you don’t recognize the sender, the email has an attachment, the email subject field is blank, or the email asks you to confirm or review information using an attachment.
Generally, once you open this attachment, a piece of malware will be downloaded onto your computer. If you unsuspectingly open the attachment and the contents of the file or document look different than what you expected, this may also indicate malware.
Darknet Email Threat
A darknet email threat is a common scam in which someone emails you pretending to be a person from the darknet—i.e., the “underground” part of the internet. Often, the email appears to have been sent from the user’s own email address. The sender states they’ve hacked your email and have been monitoring your computer for some time, accessing information on your contacts, computer use, browsing history, and so on. The sender then claims they have compromising information or videos of you and demands money to keep them from sending this information to all your contacts. This kind of threat preys on people’s fear of being exposed in their private lives and activities.
Generally, this kind of email is just a scam, but it’s possible the sender has either spoofed your email address (i.e., made it appear they sent the message from your own email address) or obtained your email, name, and password from a compromised website. It’s important to know when your credentials or identity has been compromised, so you can create new passwords and protections.
Options for Defense
Regardless of how you define an email threat, the options for defense are also rapidly expanding and developing.
There are numerous ways to defend against email threats, including implementing antivirus and mail scanning software, instituting internal policies, and using multiple levels of authentication on your account (e.g., logging in both online and via your phone). There are two basic levels to focus on when implementing security measures: first, the point before the user has received or opened the email; and second, the point at which their credentials may have been compromised.
Organizational Policies
Organizational policies play a large role in preventing users from opening suspicious emails. Any such policy should include clear and thorough education on how to recognize an email attack, and what to do if you suspect someone has targeted you. In addition, businesses should have clear policies on what staff should do if they accidentally open an email attachment or link.
Tools and Software
Another factor is using software to stop suspicious emails from reaching users. You should have in place some kind of software to identify malware attacks and suspicious emails, and a tool to detect unusual activity on the mail server.
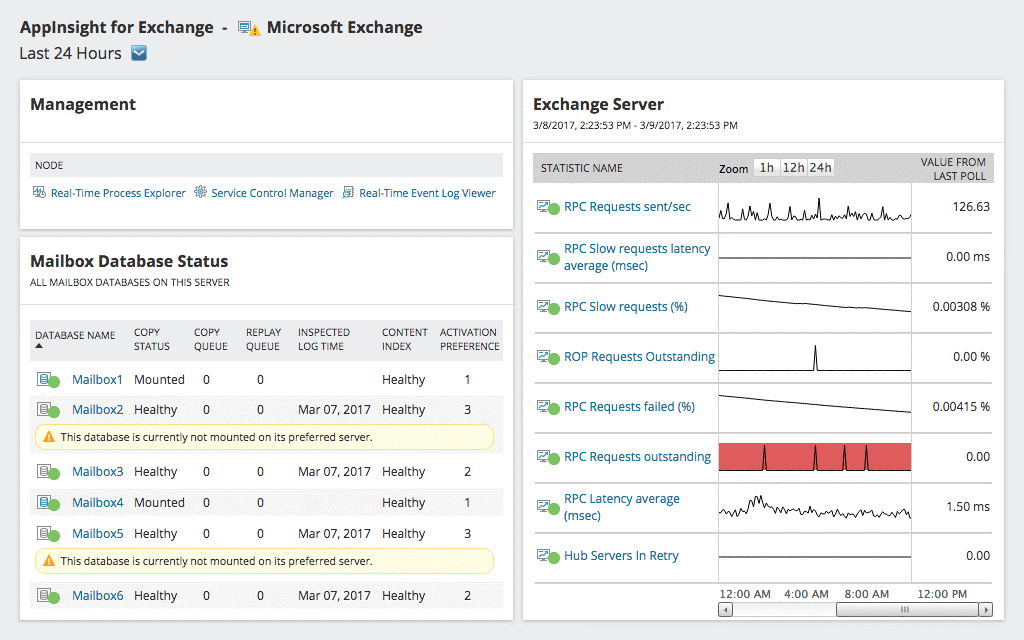
My preferred tool for protecting your business from email attacks is SolarWinds Server & Application Monitor (SAM). SAM is both email monitoring software and a mail server monitoring tool, which can help detect any suspicious activity before a breach occurs. For example, it can detect sudden email traffic spikes, which can indicate an attack is occurring.
You can access a free trial of SAM for up to 30 days.
Once a breach has occurred, it’s important to determine which accounts and credentials have been exposed, so relevant passwords and access details can be changed as quickly as possible. My top choice for protecting and securing account credentials is SolarWinds Identity Monitor, a web-based tool that allows you to enter your email address to check for corporate credential leaks. Identity Monitor notifies you when any of your employees’ credentials have appeared in a data breach or data leak posted on the dark web. This type of careful monitoring means if an attacker steals your credentials, you’ll be notified, ideally before the attacker shares the credentials with other malicious entities.
SolarWinds Identity Monitor is an annual subscription service. You can set it up to monitor for potential issues before they occur, with the option of adding domains or private emails to a “watch list.” In addition, IP addresses can be set up for monitoring and compared to known botnets: if you see one of your IP addresses linked to a botnet, you can identify this computer has had malware installed on it.
Best Tools to Fight Email Threats
Effectively fighting email threats requires a combination of employee and organizational education, wide use of tools, and security at multiple levels of your business. By implementing SolarWinds Identity Monitor and SolarWinds Server & Application Monitor, you can be sure you’re fighting threats comprehensively, and protecting each aspect of your infrastructure. Finally, make sure you have well-thought-out response and management policies set up in your organization, to ensure problems are escalated to the right person in a timely manner.
What if you need to protect more than your own organization? If you’re a Managed Service Provider (MSP) or in a similar business, you may be responsible for keeping hundreds or thousands of clients safe from constantly-evolving email threats.
In this scenario, you’ll want a tool designed specifically for your needs. Enter Mail Assure—a product from the SolarWinds family (currently N-able), but this time built with MSPs in mind. It can protect your clients from the latest email-based attacks, it’s easy to use, and it is continuously updated so that it meets the necessary security standards.
