Scanning your network regularly is important for ensuring the network and devices on it are functioning healthily. Here’s how to go about network scanning to understand what devices are on your network, view how they’re performing, and understand the traffic moving between them. There are manual ways to perform some of these tasks, but I suggest using a network scanning tool for optimal results.
1. SolarWinds® Network Performance Monitor (NPM)
2.SolarWinds® IP Address Manager
3.Holm Security Network Scanning tool
What is Network Scanning?
Wondering how to see all devices on the network? As the term is typically used, “network scanning” is the process allowing you to determine all active devices on your network. Active scanning is when the tool sends a ping to each device on the network and awaits a response. The scanner then looks at the responses it gets to see if there are inconsistencies or vulnerabilities.
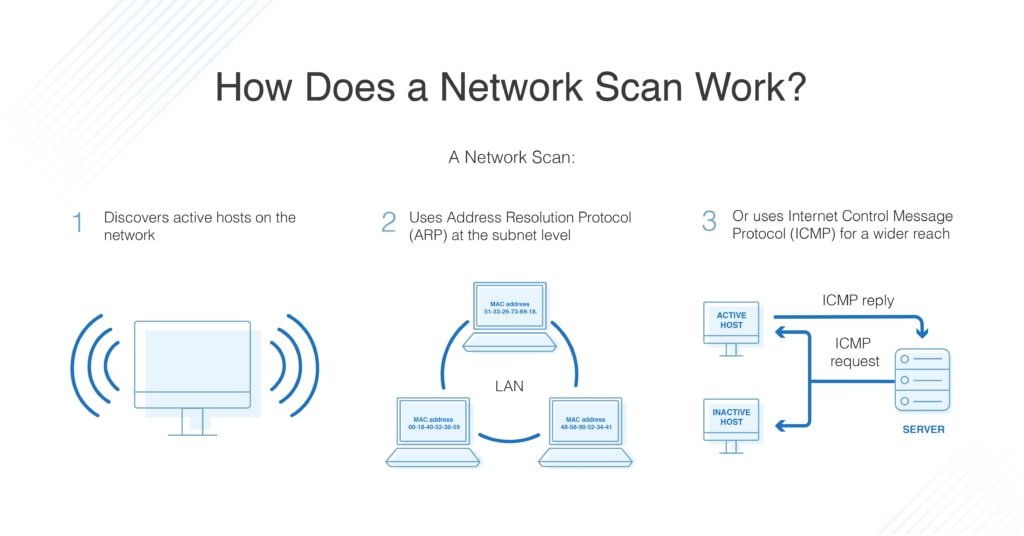
For IP networks, this is often done by sending a ping to each possible IP address and getting a response to determine its status.
It’s possible to manually ping your subnet to using an Address Resolution Protocol (ARP) scan. But to view all devices on the network across all subnets, your best bet is to use a tool that can automatically run scans and discover devices.
Using the necessary Internet Control Message Protocol (ICMP) scan is more complicated, but it can be done—you’ll need to use echo, timestamp, or subnet mask requests. This method is often used to map network topology.
The purpose of network scanning is to manage, maintain, and secure the system using data found by the scanner. Network scanning is used to recognize available network services, discover and recognize any filtering systems in place, look at what operating systems are in use, and to protect the network from attacks. It can also be used to determine the overall health of the network.
What is Passive Scanning?
Network scanning can also refer to packet sniffing, or passive scanning, which captures and tracks the traffic moving over the network in the form of data packets. If you’d like to track the packet-level traffic on your network, you’ll need to implement sensors on managed devices and applications and deploy a tool for you to easily translate packet data into intelligible and relevant information.
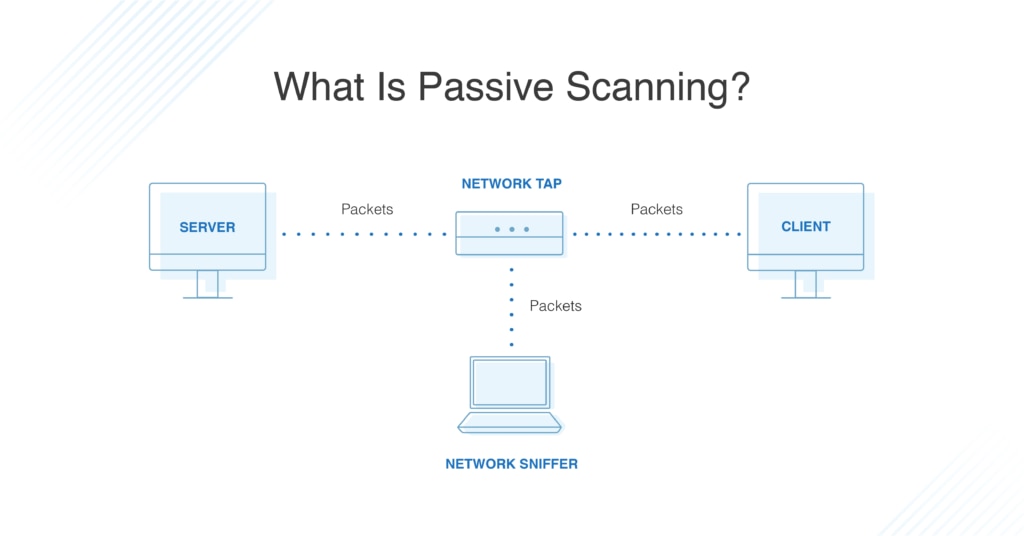
This approach looks at network information as soon as a device or system appears and starts sending messages to the network. In reality, networks release a lot of information in their normal communications, enough that passive scanners can simply look at this traffic flow, rather than pinging the devices themselves. This can help reveal traffic types, protocols, and bottlenecks within the network. It can also reveal potential security risks by catching anomalies.
Passive scanning has some limitations, as it cannot detect devices or applications that never communicate (such as unused apps and devices) and can be vulnerable to problems caused by infected systems intentionally distributing misinformation. However, it’s an important form of network scanning and should be part of your toolkit.
4 Best Network Scanning Tools
Using a network scanning tool is essential if you have more than a few devices on your network, or if your network is large enough to include multiple subnets. Trying to manually manage a large network is difficult and can expose your business to major security risks. There are several different scanning tools on the market, each with a slightly different approach to the task.
1. SolarWinds® Network Performance Monitor (Free Trial)
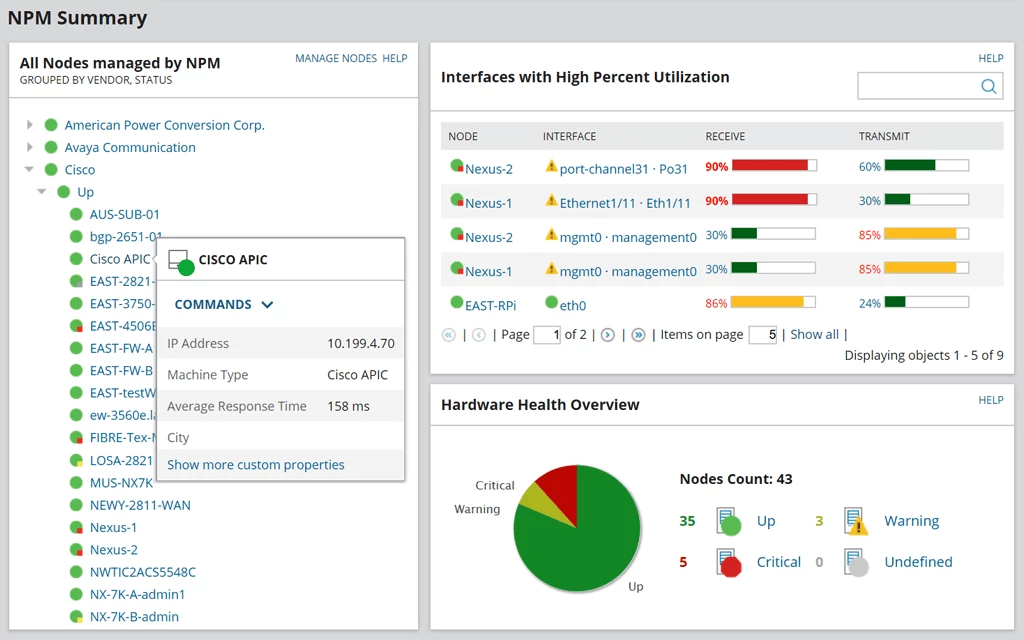
I suggest using SolarWinds® Network Performance Monitor (NPM) with its network scanning solution to automatically scan your network. This tool primarily uses passive scanning to reveal a wide range of critical network information. It functions as a network discovery and performance management tool, allowing you to determine what devices and applications are on your network and create instant network topologies. You can scan the network information to determine whether devices are performing correctly, whether they are available, or if there are any faults in the network.
NPM can examine and monitor multi-vendor networks, as well as providing you with visually pleasing network insights. I like the intelligent visualizations such as heat maps and comparative graphs, as it can help you understand your network from a node-by-node perspective. This helps troubleshoot and pinpoint problems or discover weak points that might be vulnerable to attacks. NPM can also scale to much larger environments and enterprises. I also find it to be intuitive for beginner users—figuring out how to use NPM isn’t difficult.
2. SolarWinds® IP Address Manager (Free Trial)
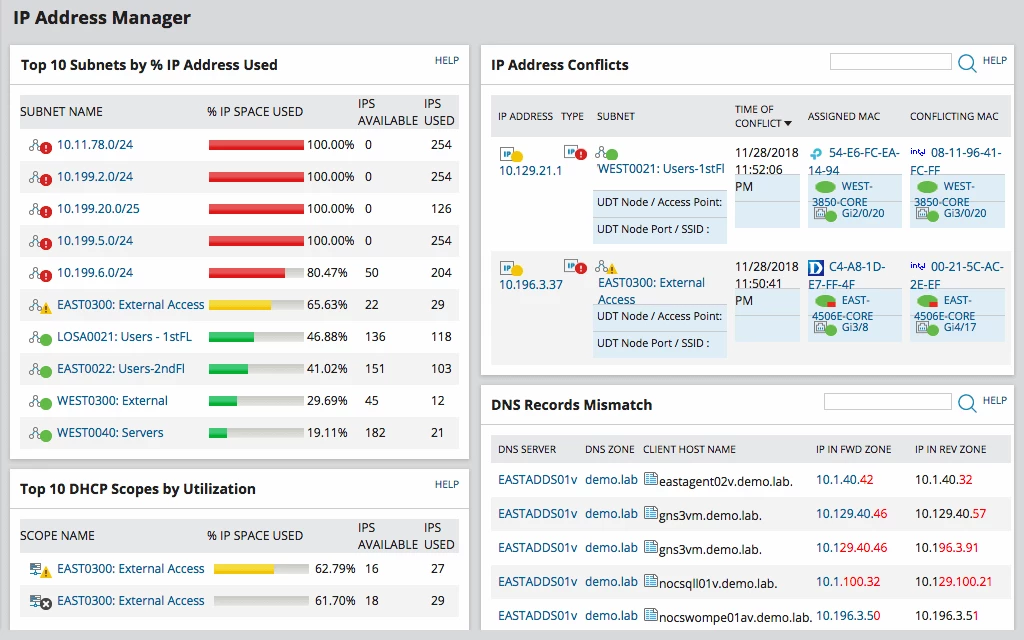
If you’re looking for IP address network scanning, you should consider another SolarWinds tool—IP Address Manager (IPAM). This tool is more focused on managing and discovering devices based on IP information, even across subnets. In terms of tracking performance and traffic, NPM is the more robust tool, but it’s also useful to be able to manage your IP addresses, especially on a large network. If you’re looking for this kind of network scanning, I’d give IPAM a shot.
3. Holm Security Network Scanning Tool
Another passive scanning tool you should consider is Holm Security Network Scanning tool. This tool automatically and continuously scans your network to search for vulnerabilities. In particular, it looks at issues such as weak passwords, misconfigured systems, old software, and exposed services and functions. It also allows you to scan your entire network over different local environments and create a map of your network. You can then prioritize, organize, or remedy vulnerabilities.
4. Swascan Network Scan
Similarly, if you’re looking for effective packet sniffing, Swascan Network Scan tool is also useful. First, the interface is engaging, clean, and very simple to use. With high-quality data analysis and graphs, Network Scan tool provides complex information about vulnerabilities in your network. The reports and accompanying managers can then assist you with fixing these errors through their detailed action plan.
Network Scanning Today
If you’re wondering how to scan your network, first take the time to understand which type of scanning you need. Managing IP addresses and devices? You might be able to get away with manual IP scanning, but there are many easy-to-use IP manager tools out there. Performing packet sniffing is more complicated but is a critical task to ensure you have network oversight. This means implementing the right sensors and a tool that translates packet data into easily readable information. To manage network issues and scan for potential problems, I recommend the SolarWinds Network Performance Monitor due to its scalability, heat map visualizations, clean interface, and an extensive set of tools.
