Is there a silver bullet for making policy and risk compliance easier? While no single solution can manage compliance end-to-end, the answer may surprise you. But first a little background.
Introduction
Risk Management is fundamental to maintain a successful enterprise. The purpose of Risk Management is to identify uncertainties, hazards, exposures, liabilities, and other risks which may cause harm to the organization, forecast the potential impact, and then implement measures designed to reduce these effects. Considering IT operations is vital to business continuity, it should be no surprise Risk Management is a central tenant of IT governance.
One of the tools used to manage risk is the Risk Policy. In IT, the risk policy is a top-level document specifying what standards the organization will observe to safeguard the confidentiality, integrity, and availability of its IT systems and data. The Risk Policy will often include additional sections addressing security and any obligations to industry and regulatory mandates like Payment Card Industry Data Security Standard (PCI DSS), Health Insurance Portability and Accountability Act (HIPAA), and similar.
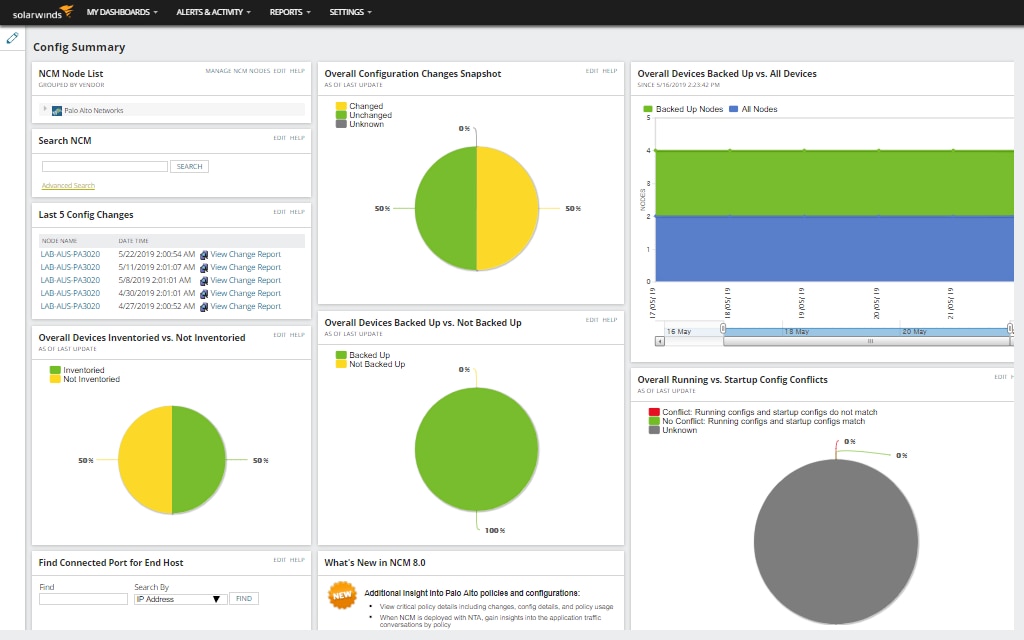
Cisco Policy Report provided by SolarWinds® Network Configuration Manager (NCM):

Policy standards define what safeguards will be required but not how a standard will be implemented. For example, the PCI DSS policy has a standard that states that the organization will “install and maintain a firewall configuration to protect cardholder data.” However, it doesn’t specify what type of firewall to use, what firewall rules to deploy, or what it means to maintain the firewall, which leads us to our discussion on controls.
Policies are operationalized by implementing controls which support policy standards. There are two primary types of controls: technical and procedural. Procedural controls are “managerial” or “operational” in nature. They define how people are to perform a task or job function. For example, an IT manager will retain a full system backup for seven years. On the other hand, technical controls are directly implemented on IT systems using supported configuration options. For example, a server shall be configured to require a logon password. Once technical controls are in place, the challenge becomes to keep them in place. This leads us to the topic of compliance.
Policy compliance seeks to verify all controls, as defined by policy, are: 1) implemented and 2) remain operational as implemented. As such, policy compliance can be thought of as a “continuous process”—one of implementation, monitoring, and verification. While it’s common to think compliance is something an auditor does, in reality IT operations is responsible. An auditor only independently verifies policy objectives are being met.
As mentioned earlier, technical controls are implemented as configuration options. And more specifically, network controls are implemented as configuration options in network routers, switches and similar devices. So, perhaps the best risk and policy management tool in your toolbox is your Network Configuration and Change Management (NCCM) software. By definition, NCCM software manages configuration changes and protects configurations and devices from unwanted changes.
Since the network forms the core foundation for IT services, and the quality of network service is defined by the configuration of its constituent routers, switches, controllers, access control devices, and more, then it makes sense to carefully manage and monitor these configurations. This is why NCCM plays such a critical role in IT operations and risk management.
So just how does NCCM accomplish all this? Here is a quick overview.
Configuration Management
Device access – Perhaps the first place to start is by removing ad-hoc access to devices. An NCCM can help you eliminate ad-hoc (unauthorized) device access and require configuration changes to be made using the NCCM management console.
Change control – By requiring all configuration changes to be made using the NCCM console, you can assign administrative privileges and implement a formal change review and approval process. This eliminates unplanned and unauthorized actions and maintains a history of changes made.
Configuration templates – An NCCM allows you to create a standardized script or change template for making reoccurring changes. This ensures changes will be uniformly made as approved. Configuration change templates are device and vendor-neutral. They provide an automated way to mass-deploy new services or quickly remediate a policy violation or security vulnerability across the network.
A simplified view of policy violations from SolarWinds NCM:

Job scheduling – Want to control when changes are made? An NCCM provides job scheduling to execute changes during maintenance windows.
Backup and recovery – Hardware failure and human error can break your network. Recover from these disasters quickly. An NCCM can schedule, back up, find, and restore device configurations.
Configuration Monitoring
Change detection and analysis – You’ve spent time and effort getting your configs to a baseline. How do you know when something changes? What if a change is made to the running config but not saved to the startup? An NCCM can monitor device configurations and notify you when any change is made. You can even compare two configs side by side and see what statements were added or removed.
Configuration Auditing
Audit Policies – Want to help ensure your configs contain (or don’t contain) specific configuration statements? An NCCM policy can be used to identify what is expected (or forbidden) in a configuration. Policies are useful to verify compliance with internal policies as well as DSS PCI, HIPAA, SOX, DISA STIG, and other industry mandated policies.
Remediation – An NCCM helps you correct violations fast with remediation scripts (defined as part of the policy).
Summary
Change management, monitoring, and auditing are three ways an NCCM helps you manage and protect your network configurations as well as manage IT risk.
Using SolarWinds Network Configuration Manager (NCM), you can manage your network configurations and many of the procedural and technical controls for your network to help inform your risk policy.
To learn more about Network Configuration Manager, visit the NCM product page. To learn how to write an NCM policy, read this THWACK® blog post.
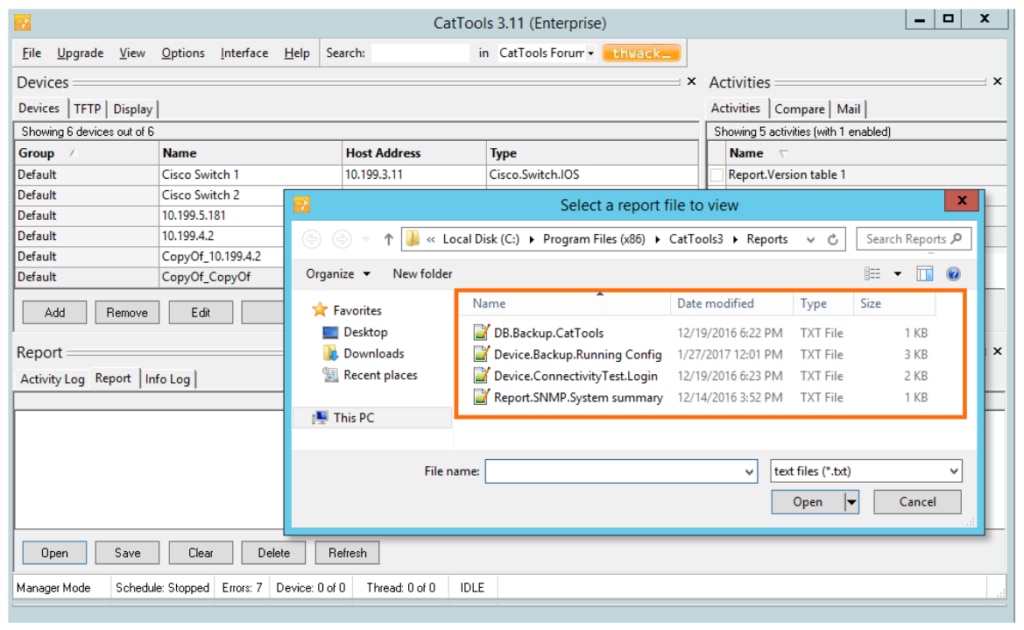
If you’re looking for a more lightweight change management solution, Kiwi CatTools® is designed to provide small business networks with affordable, yet powerful network automation and configuration management features. Kiwi CatTools can allow you to easily push configuration changes, track network devices changes, rollback to previous configurations, and automate backups on routers, switches, and firewalls. A free 14-day trial is available.